Remove Moatads virus (js.moatads.com) in Chrome, Firefox and IE
The browser redirect routine involving z.moatads.com and js.moatads.com is advantageous for merchants who thus advertise their products, but it’s a headache for end users who repeatedly visit landing pages with annoying recommendations. When dissecting these instances, researchers discovered that they are sustained by adware, which is a category of mild-impact infections hijacking browsers to capture web traffic and display ads.
There are scripts sanctioned by website owners. This type of marketing usually complies with rigid regulations in terms of the amount of advertising and the way it is presented to visitors. There are also adverts that exist outside these rules, where potentially undesired applications spawn popup windows at random. The fundamental difference between the above-mentioned two clusters is where the intrusive promo content originates: on the web server end, or from within a specific computer system. This post is going to focus on infection incidents caused by an adware strain. The attackers pull off these attacks using a hijacker known as Moatads.
The crooks distributing this adware employ a tactic that makes the app resemble a legitimate web marketing analytics solution. The operation of Moatads on a computer, though, is hard to call useful. It triggers splash screens and generates ads on nearly all websites the infected user goes to. In particular, it may inject sections with deals on top of original content. The victim will also run the risk of accidentally clicking inline text that may link to malicious pages with cross-site scripting vulnerabilities. The adware also appends regular search engine results with additional sponsored entries. Furthermore, interstitial promotional windows will be popping up in the background once in a while. Browser brand doesn’t matter as the bug is universal enough to affect IE, Chrome and Firefox alike.
Moatads is installed surreptitiously. Users don’t get much chance to realize that the intrusion is happening until the adware starts playing havoc with their PCs. Bundling is the technique that makes this stealth real. Freeware offers often come along with extras that aren’t necessarily safe. By default, the co-conspirator program installers suggest the express (recommended) option which presupposes the package principle. If a user doesn’t opt out of this mode during the setup of some cheesy video converter or file downloader, the drive-by will take place and the unwanted changes will be automatically made to the system in the blink of an eye.
Adware troubleshooting tends to be a challenge. These apps shouldn’t be treated like regular ones when it comes to the uninstalling routine, because they simply resist standard removal methods. To get rid of Moatads redirects and popups completely, read the follow-up and stick to the procedure that proved to work.
Table of Contents
Moatads adware automatic removal
The extermination of Moatads hijacker can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the adware removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the adware is gone for good.
Remove Moatads adware using Control Panel
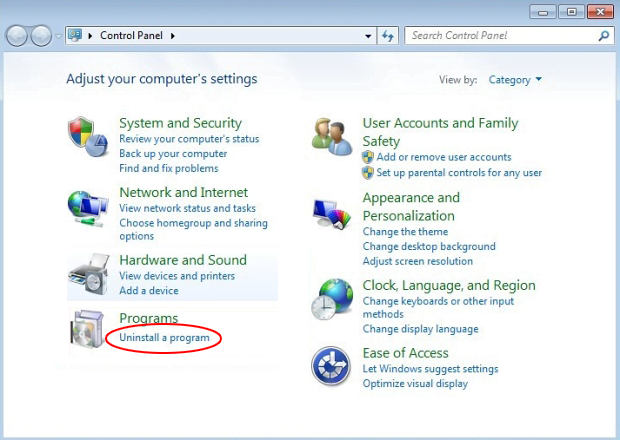
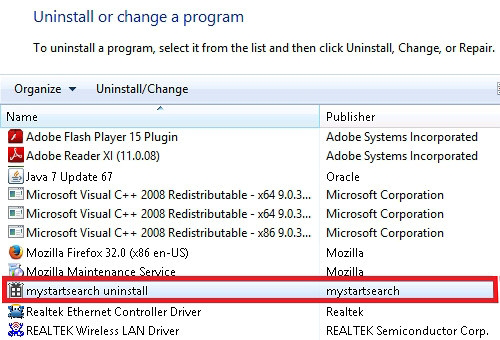
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Moatads adware removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
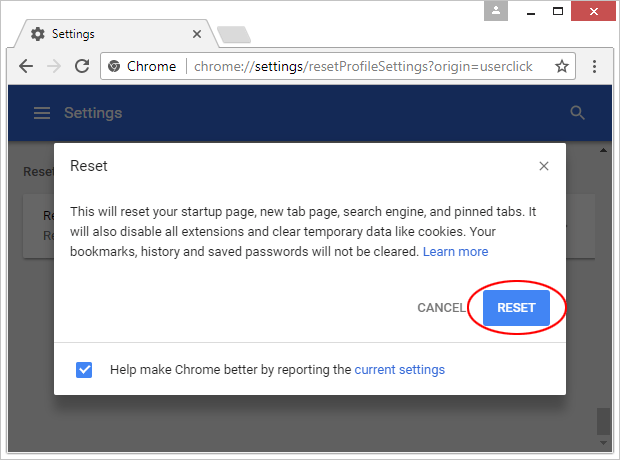
Reset Google Chrome
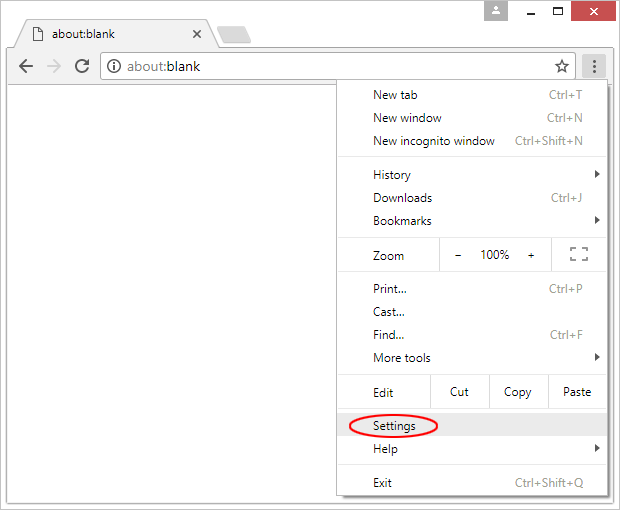
- Click on the Chrome menu icon and select Settings

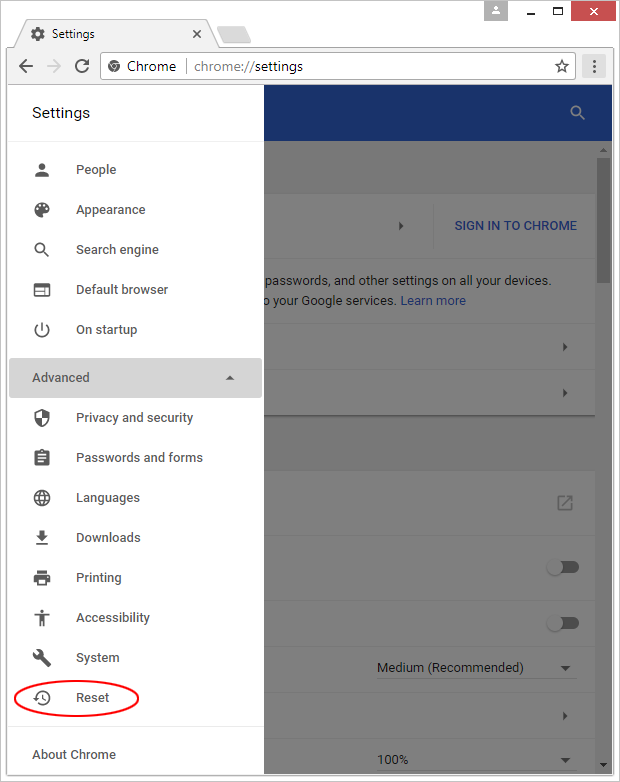
- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

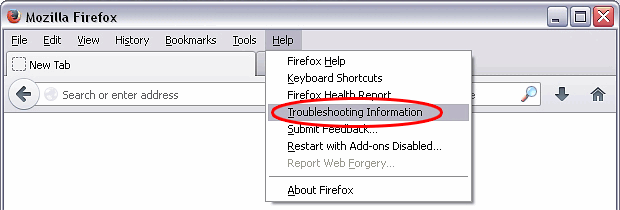
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

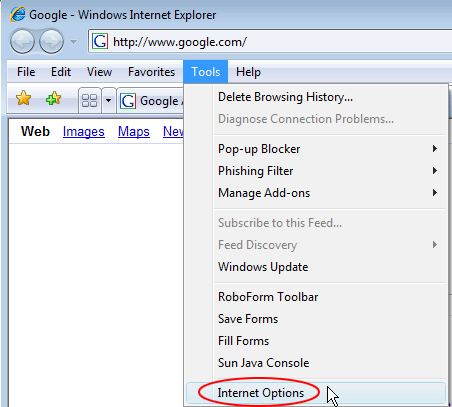
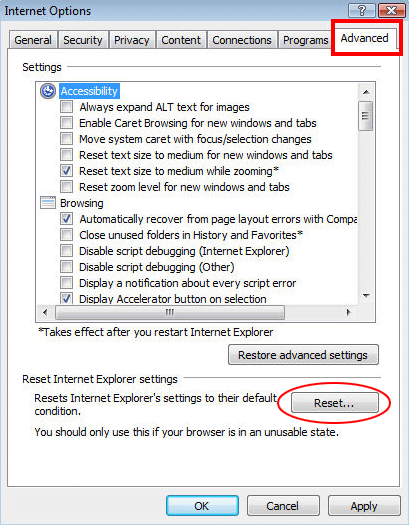
Reset Internet Explorer
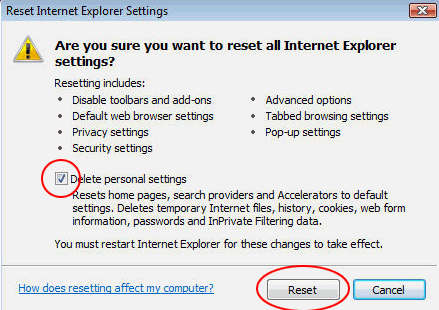
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether Moatads adware has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this hijacker are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓