Remove .micro virus file extension encrypted by TeslaCrypt 3.0

An increasing number of Windows users have been discovering that the extensions of their personal files get changed to .micro out of the blue. This is only one of the many symptoms of a ransomware attack by the new edition of TeslaCrypt 3.0, a crypto virus that locks one’s data and extorts money in exchange for decryption. The most recent 3rd generation of this threat gets its victims into a perplexing situation where the only effective way to redeem the files is to pay.
TeslaCrypt has been known for almost a year at this point. It started off as a somewhat unordinary ransom trojan that targeted data related to computer games along with the regular personal files. Followed by the Alpha Crypt copycat shortly after emergence, the infection eventually continued its malicious crusade under the initial name and got a couple of updates rolled out ever since. Each new iteration would include a number of bug fixes that were found by security community, but the latest version turned out the most advanced one. Researchers previously devised a recovery utility called TeslaDecoder, which was able to decrypt the items that got the following extensions appended to them on the infected PCs: .ecc, .exx, .ezz, .xyz, .zzz, .aaa, .abc, .ccc and .vvv. The fresh build of the trojan adding .micro strings to files, unfortunately, cannot be combatted this way.
The specificity that allowed restoration earlier was a key handling flaw missed by the fraudsters. Since the ransomware uses AES standard to conduct encryption, the public and private key are the same. One of the files storing the key (key.dat or storage.bin) was kept on the contaminated computer, which enabled the above-mentioned tool to find the details required for decrypting the info. In the case of the variant adding .micro, .ttt or .xxx extensions, the key exchange workflow has been changed so that this technique is inefficient. The key is no longer left on the machine – instead, it gets sent to a secure server controlled by the bad guys.
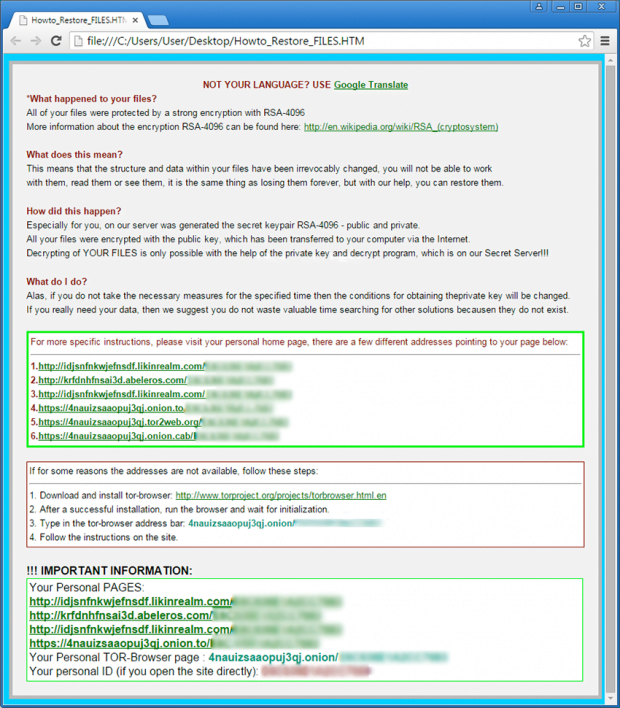
This ransom trojan communicates with the victim by displaying its main application pane, changing the wallpaper and dropping several instruction files on the desktop. In particular, the user can open one of these three documents to get further directions: Howto_Restore_FILES.TXT, Howto_Restore_FILES.BMP or Howto_Restore_FILES.HTM. According to these notes, the user should navigate to his or her ‘personal home page’ by clicking one of several available links, including a Tor gateway.
The page titled ‘Decryption Service’ provides information about the ransom amount to be submitted, which is currently set to about 500 USD, and lists the rest of the steps to send the money in Bitcoins, retrieve the private key and reanimate the data. It’s worth admitting that the criminals are doing a good job covering their tracks. They resort to The Onion Router service for anonymity of interactions with the infected people, and they only receive payments in cryptocurrency to avoid stalking and thus get around issues with law enforcement.
At first glance, it seems that following the scammers’ demands is the sole way to regain access to the .micro files. The decoder doesn’t help, and the buyout may be unaffordable. And yet, recovering the information in this case isn’t all wishful thinking – the users can try some methods relying on special software and native features of the operating system.
Table of Contents
TeslaCrypt 3.0 extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download TeslaCrypt 3.0 file remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by TeslaCrypt 3.0 extension
Workaround 1: Use file recovery software
It’s important to know that the TeslaCrypt 3.0 extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether TeslaCrypt 3.0 extension has been completely removed
Again, file removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓