How to remove Memz trojan virus from Windows

Most computer viruses are written for specific malevolent objectives, typically ones related to financial gain in one way or another. Infections like the Memz trojan, however, go beyond this mercantile paradigm. The above-mentioned app appears to be built for wreaking havoc with any Windows machine it ends up on, period. It calls forth multiple glitches and bizarre visual effects, rendering the contaminated computer virtually inoperable at the end of the day.
Table of Contents
What is Memz trojan download
The Memz trojan was originally designed as a proof-of-concept viewer-made malware. Its name is a leetspeak variant of the term “Memes”, which basically reflects a lot of what it does to a contaminated PC. There is more to its activity than mere pranks, though. Some of the nasty effects include random apps popping up, weird web search queries being automatically looked up in the browser, the mouse cursor gradually going nuts, and many more things that the average user will hate to witness on their workstation. One of the most destructive things that Memz can do to a computer is the overwriting of the first 64 KB of the hard disk, which affects the Master Boot Record and thus requires advanced troubleshooting through bootable recovery media. Luckily, this feature is not universal and it’s restricted to the most aggressive variant of the pest only.
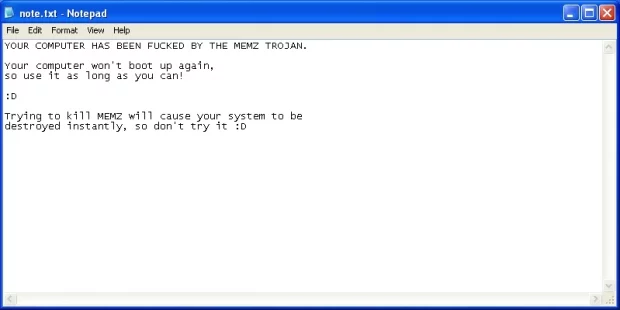
Similarly to the nefarious case of Hidden Tear and EDA2 ransomware built for educational purposes, the source code for the Memz trojan was made available to the public. A user nicknamed Leurak posted the entirety of this information on his GitHub page a couple of months ago. This means that ill-minded ne’er-do-wells can take the readily available code and deliver it to users via spam or bundled freeware installations. The payload is available as an executable (.exe) or a batch file. Once triggered, it displays note.txt Notepad window with a warning message in it. The alert says, “Your computer won’t boot up again, so use it as long as you can! Trying to kill Memz will cause your system to be destroyed instantly, so don’t try it.”
This spooky notification will be followed by the default web browser being haphazardly opened without any such action on the user’s end. It will display random websites or search results for various odd queries, for instance “what happens if you delete system32” or “Internet Explorer is the best browser”. The impact tends to get yet nastier. The victim starts noticing the mouse cursor move on its own, and the operating system begins generating error messages and attendant bleeping sounds. On the next stage of the attack, Memz inverts screen color every second. Finally, the infection will be making snapshots of the screen and display those at a growing rate as part of the tunnel effect.
Rebooting the computer triggers the final Memz payload, where the user will see the following message, “Your computer has been trashed by the Memz trojan. Now enjoy the Nyan Cat…” Indeed, then comes the Nyan Cat animation and sound. It goes without saying that using a machine compromised by such a disruptive malware is pretty much impossible. The victim can use the “taskkill /f /im MEMZ.exe” command to terminate the trojan, but the system will remain messed up because of the damaged MBR and partition table. The use of Windows installation disc should address the issue. If you realize that this bug is on board when it’s just beginning to cause trouble, don’t fail to use the steps below to keep it from going further.
Memz trojan automatic removal
The extermination of Memz trojan can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the trojan removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the trojan is gone for good.
Posted in: KnowledgeBase
Leave a Comment (0) ↓