MegaCortex crypto virus: ransomware decryption and removal

Ransomware campaigns are gradually mutating towards a targeted approach and a larger attack surface. Few present-day lineages are going after individual users – instead, the focus is on big enterprises that can afford to pay fortunes just to get their proprietary data back. The new sample called MegaCortex fits the mold of such a novel modus operandi.
Table of Contents
What is the MegaCortex ransomware?
Which way is the ransomware plague heading? This is kind of a tough question, given the numerous cyber gangs in play, plus the discrepancies between different strains of the perpetrating code. There is some common ground, though. The most conspicuous vector of the evolution comes down to targeted attacks, as is the case with a specimen called MegaCortex. Originally spotted in May 2019, this family has been plaguing business networks and its wicked operators have reportedly had some success. However, it’s not until early August that this wave grew into a real disaster. The latest variant of MegaCortex, which appends the .megac0rtx extension to hostage files, has made quite a few high-profile victims, with the lowest demanded ransoms amounting to 2 Bitcoin, or over $23,000. On top of that, the infection now leverages clever evasion and persistence techniques allowing it to do the most damage with the smallest possible chance of being stopped in its tracks once the incursion has begun.
The distribution of MegaCortex ransomware is composed of a series of events. First, the crooks gain a foothold in an enterprise environment by hacking the domain controller, a server that handles user authentication within the network. There is very little known about the specific mechanisms of this exploitation at the time of writing, but the fact is that the attackers obtain sufficient privileges to run arbitrary processes remotely behind the admins’ backs. The next move engages the PsExec utility to disseminate the offending code from the enslaved domain controller to other computers on the same network. The deleterious binary used in the recent attacks is called winnit.exe. The authors of this strain were able to somehow get a valid digital certificate for their code, consequently they don’t have to obfuscate the unauthorized encryption part of the onslaught via multiple scripts that would otherwise need to be fired up in several stages. All in all, the wrongdoers get to the cryptographic phase of the breach in a very sneaky and sophisticated fashion.
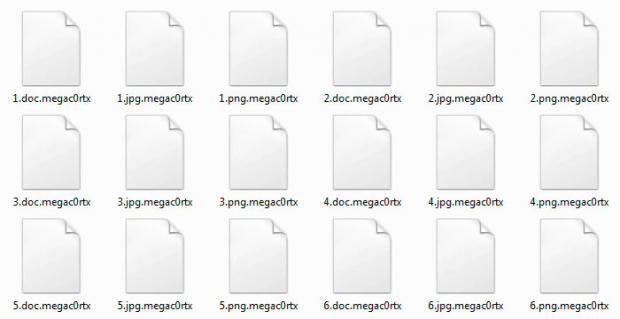
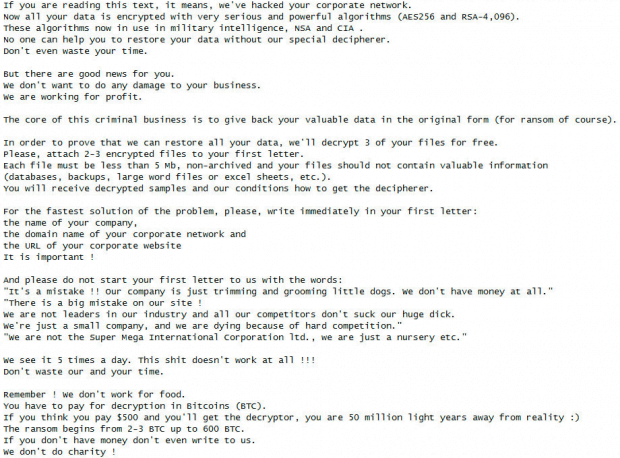
Having found the entirety of valuable files on the compromised hosts, MegaCortex applies a cipher to lock them down. As a byproduct of this workflow, it concatenates the above-mentioned .megac0rtx string to each encoded entity while leaving the original filenames intact. So, if an image Selfie.bmp undergoes the impact, then it gets renamed to Selfie.bmp.megac0rtx. The ransomware also drops a rescue note onto the desktop – this document named !!!_READ-ME_!!!.txt contains the ins and outs of the paid data recovery. In a nutshell, it uses fairly austere tone to instruct the victim to complete the buyout of the decryption solution and the relevant secret key. Again, the sum is astronomical and may be as high as hundreds of Bitcoins, with the upmost threshold of 600 BTC being mentioned in the criminals’ message. That’s millions of dollars, which could potentially be extorted from a major organization that fell victim to the electronic parasite in question.
There are several more unsettling facets of the MegaCortex blackmail virus that are worth mentioning. One of them is that the pest terminates more than a thousand Windows services and processes before getting down to the data encryption routine. The goal is to prevent security tools and backup solutions from interfering with the flow of the attack. The culprit also skips a handful of Windows directories and file types when looking for objects to be encrypted. This quirk ensures that the virus-tainted machine continues to function, except that the stored information becomes inaccessible. Yet another trait of MegaCortex is that it is likely to tailgate into business networks alongside notorious info-stealing Trojans codenamed Qakbot and Emotet.
Obviously, all the facts regarding this ransomware add up to form an ugly big picture: it is one of the nastiest in-the-wild threats of its sort. Hardening the defenses of corporate IT infrastructures is now more important than ever before, given the rapid shift in the popular cybercrime model. In case the attack has already occurred, be sure to eliminate the dangerous code and try some of the best practices of data recovery to reinstate the most valuable records.
MegaCortex ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download MegaCortex ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by MegaCortex ransomware
Workaround 1: Use file recovery software
It’s important to know that the MegaCortex ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether MegaCortex ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓