Remove Launchpage.org virus from Chrome, Firefox and IE

Almost like regular goods, Internet traffic is a commodity that’s subject to buying and selling these days. Online marketing is a great thing contributing to the success of various merchants and other interesting parties, but unfortunately it’s got a shady side. Some cybercrooks, such as those behind the Launchpage.org malvertising wave, engage in intercepting traffic to make money at the expense of computer users’ browsing experience.
Table of Contents
What is Launchpage.org?
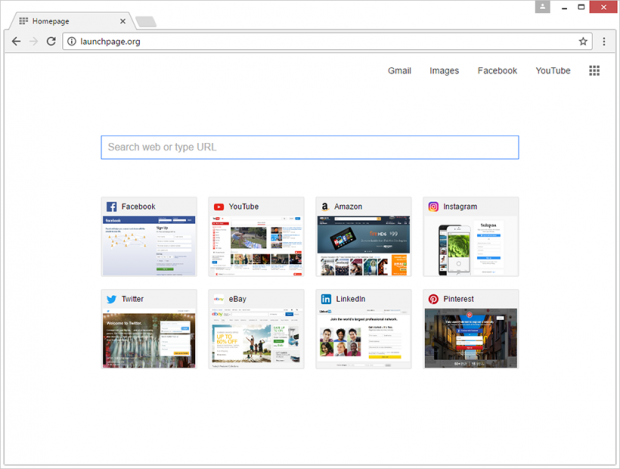
On the face of it, Launchpage.org appears to be a close replica of the average search provider. It has an embedded search bar as well as icons for popular social networks, including Facebook, Twitter and LinkedIn; streaming video and e-shopping services. The top part of the window is occupied by clickable buttons duplicating some of the above-mentioned resources, plus Gmail and image search. Overall, the site produces a perfectly normal first impression. However, the way people visit it has hardly anything to do with commonplace web surfing routine. Launchpage.org gets automatically configured to open up as one’s default homepage, new tab and preferred search engine. What is more, the victims are never asked for authorization to make these drastic changes.
While bearing a resemblance to a new tab page in Google Chrome, the website in question is actually a link in an intricate malvertising chain. This campaign also involves a rogue browser plugin or extension that gains privileges high enough to modify online preferences in Chrome, Firefox and Internet Explorer without asking for user’s consent. By taking control of these critical settings, the perpetrating program reroutes traffic to Launchpage.org every single time the user opens the browser, triggers a new tab within the same window, or tries to look up an arbitrary keyword or phrase via the URL area. No matter how many times a victim enters the correct Internet preferences manually, the hijacker will make configuration of its own take effect the next time the browser is launched. Interestingly, when searching for something through the search box built into the imposed page, users get rerouted to Google.com. This fact suggests that the malicious service under consideration has no actual data lookup engine or algorithm behind it. It is simply a worthless intermediary that monetizes user hits obtained in an unethical way.
The Launchpage.org adware infiltrates computers by means of an old school technique called bundling. This scheme is okay per se, enabling freeware publishers to make a living by spreading other apps alongside their products. However, cybercriminals may take advantage of this routine by adding their corrupt software to these compound installation clients. So every time you are up to installing a new free media player, movie downloader and the like, be sure to check whether there are extra offers included in the default setup workflow. If infected with the Launchpage.org baddie, follow the adware removal procedure below. After eliminating the potentially unwanted application, just define the desired browsing preferences and move on with your day.
Launchpage.org adware automatic removal
The extermination of Launchpage.org hijacker can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Launchpage.org remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the adware removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the adware is gone for good.
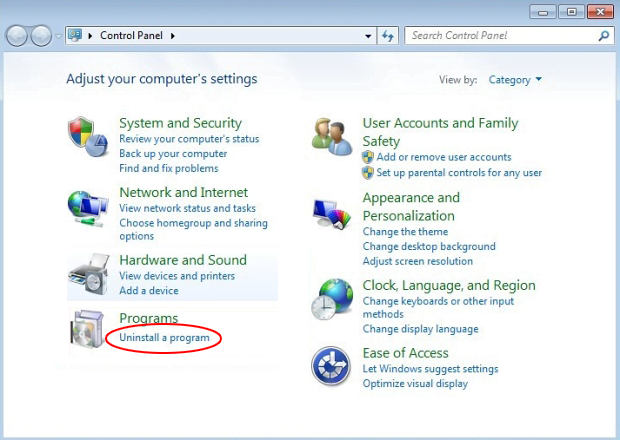
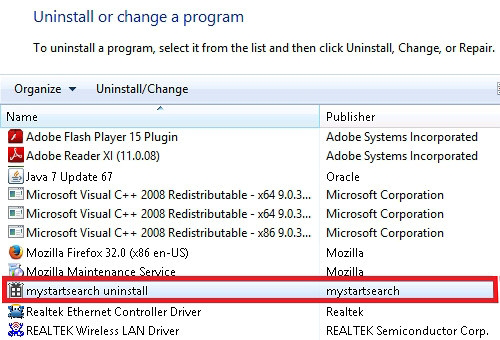
Remove Launchpage.org adware using Control Panel
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Launchpage.org adware removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
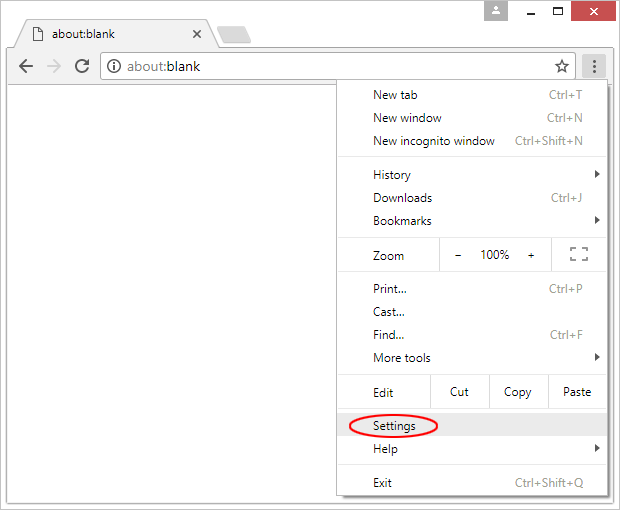
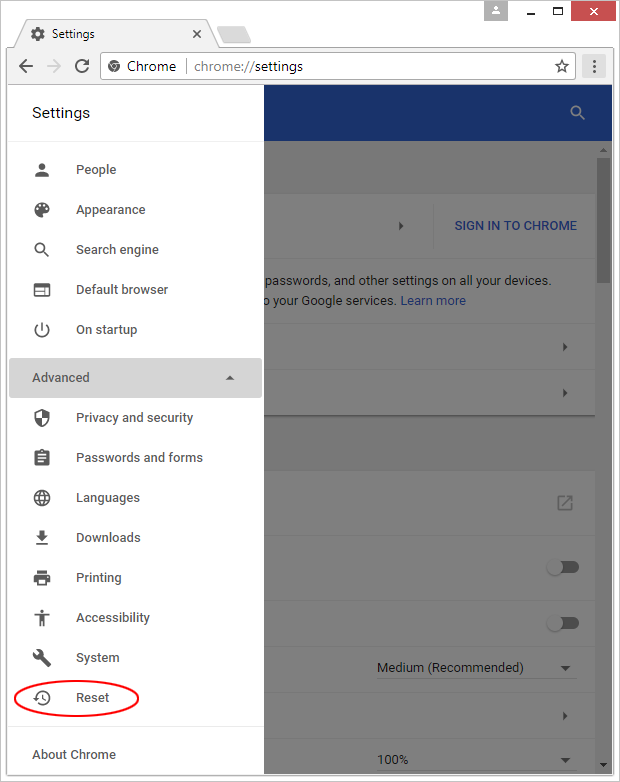
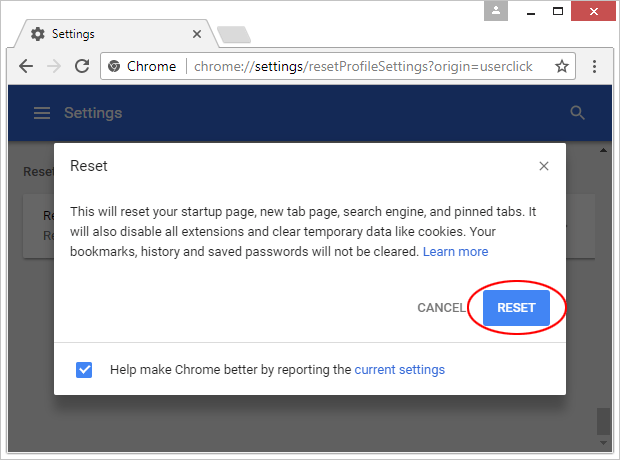
Reset Google Chrome
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

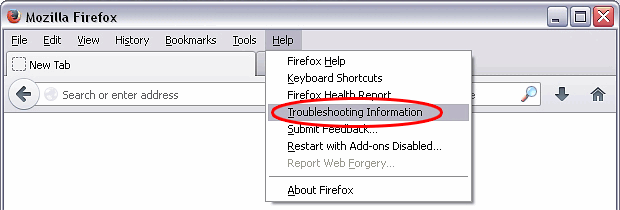
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

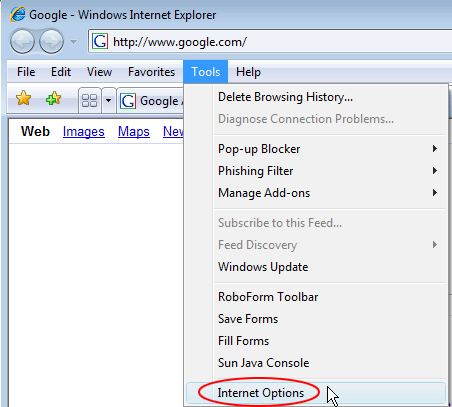
Reset Internet Explorer
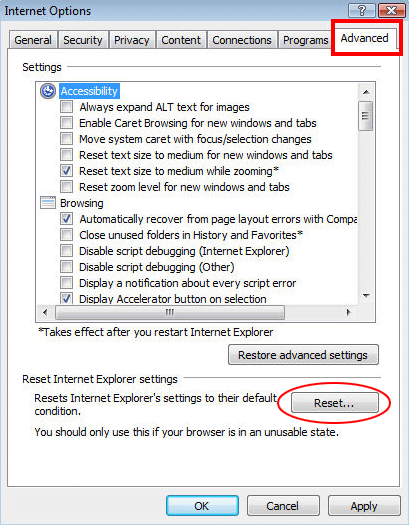
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

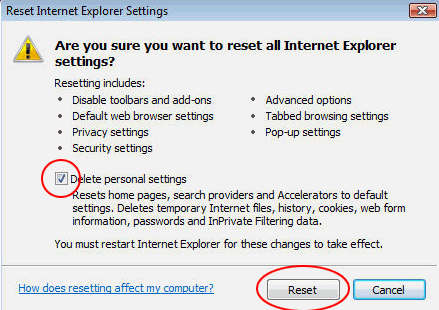
- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether Launchpage.org adware has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this hijacker are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓