How to uninstall KNCTR program from Windows computer

Technically, the application called KNCTR is supposed to be Itibiti Ventures Inc useful contrivance that allows anyone who installs it to make free telephone calls to the United States and Canada, enjoy continually updated multimedia content, and integrate their social media accounts into a single pane. Although this seems like an incongruous mix, the oddity of the program in question is a trifle compared to the malicious flip side of it.
Table of Contents
What is KNCTR
KNCTR by Itibiti Inc. is quite a bizarre piece of software, indeed. Some users may find its feature set enticing, and some are probably at their wit’s end trying to understand what phone calls have to do with fresh video content and social networks. One way or another, there is a blot on the landscape around this applet – it often appears on Windows computers without users’ clear approval. One of the installation modes that its authors chose to adopt is called bundling, which implies a blatant lack of transparency and disrespect for one’s freedom of choice. The loader for this application accompanies setup packages, where people think they are about to install an edition of Adobe Flash Player, Daemon Tools, a video converter or some free movie player, but it turns out there is an extra component under the same umbrella. The trick is all about incorporating unwanted entities into the express, or default, installation option, which some people never deselect.
At the end of the day, KNCTR will be loaded on the machine along with user-defined startup entries during every boot instance, despite the fact that the admin didn’t configure it that way. To add insult to injury, the app may add a toolbar, plugin or other extension to all web browsers that it detects on the system. This rogue add-on does not require authorization to install and run either. The associated interference, however, tends to get obtrusive. The victim will keep stumbling upon advertisements online that shouldn’t be there. These include floating adverts with coupons and freebies, comparison shopping objects, banners, in-text links, as well as full-page interstitial ads. Moreover, these items mostly extend over the authentic website graphics and text. This effect is called forth by the generation of a virtual layer that overlaps everything else on visited pages.
In addition to the visible facet of this adware’s impact, there is ongoing information harvesting in the background. To obtain data about the user and display targeted ads, KNCTR accesses sensitive details, such as the browsing history, cookies, and the IP address to derive geolocation. This isn’t quite an instance of identity theft, but it certainly infringes the infected user’s privacy. In a bid to stop this nuisance, some victims try to go the regular path and uninstall KNCTR using Control Panel. This method doesn’t work, though. It takes a specially crafted adware removal methodology to get rid of the ads and thwart privacy violation.
KNCTR ads automatic removal
The extermination of KNCTR adware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the ads removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the ads is gone for good.
Remove KNCTR ads using Control Panel
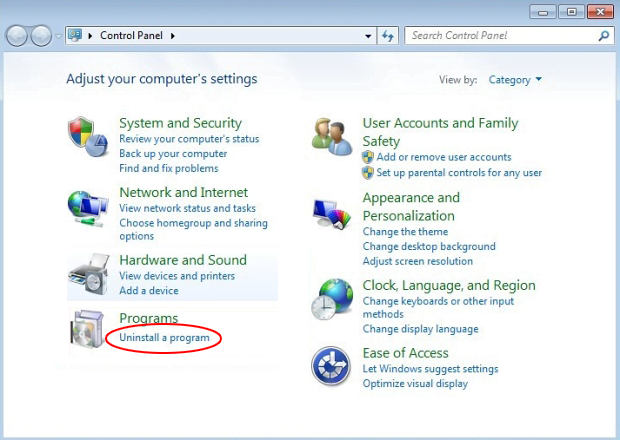
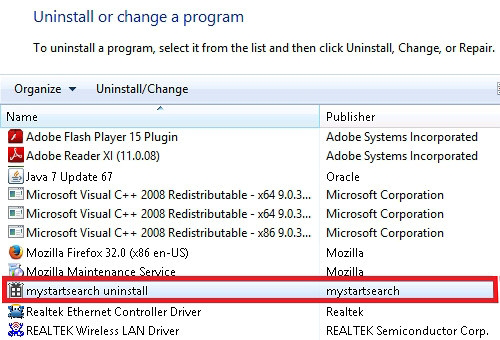
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

KNCTR ads removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
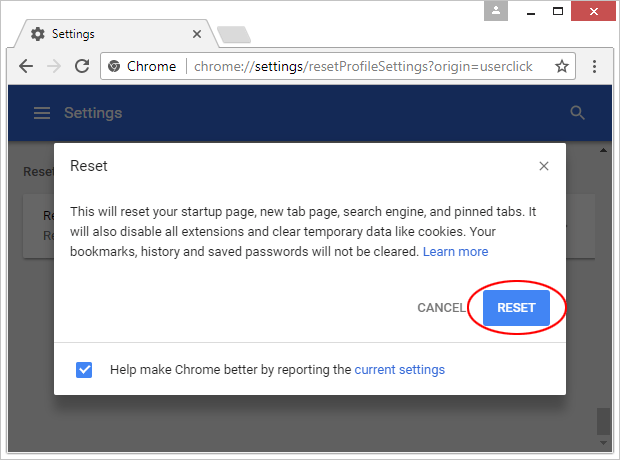
Reset Google Chrome
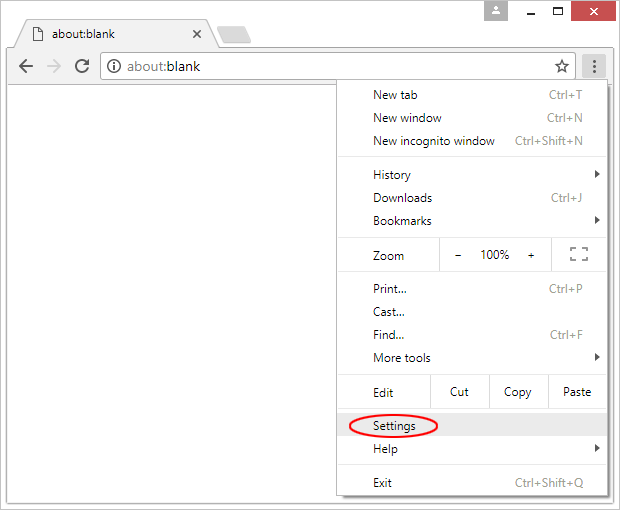
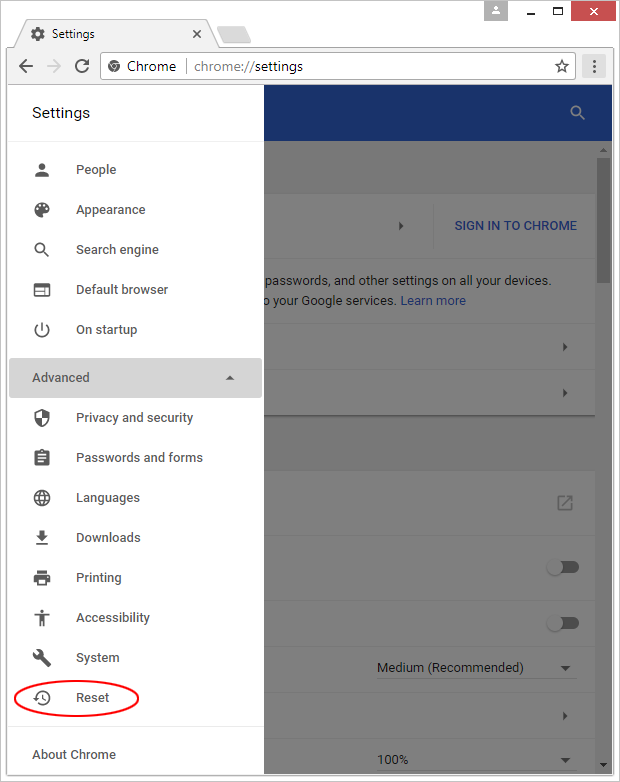
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

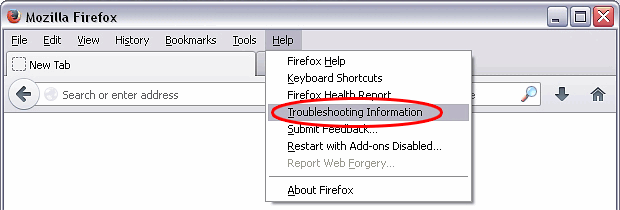
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

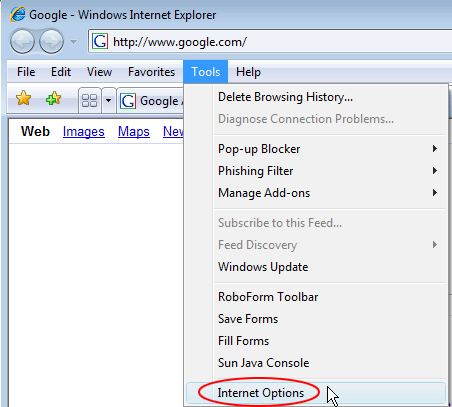
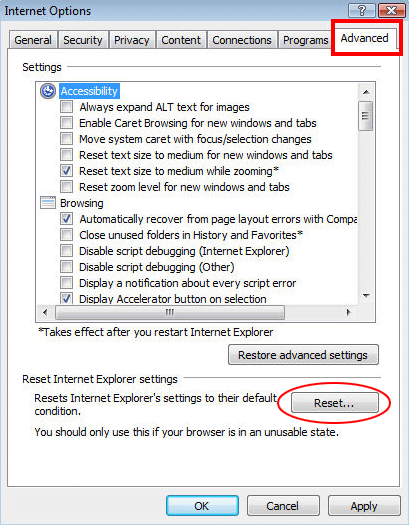
Reset Internet Explorer
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

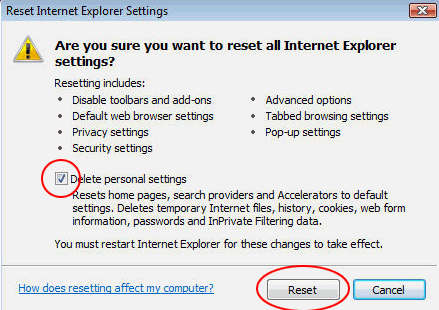
- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether KNCTR ads has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this adware are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓