How to remove KillDisk ransomware (troj_killdisk.iub virus)
Some organizations headquartered in Latin America have recently felt the destructive impact of the new edition of the KillDisk ransomware. This strain gained notoriety for involvement in sabotage campaigns where infected companies’ proprietary data got erased without the slightest change for recovery. Learn how the latest variant of this virus acts and how to avoid it.
Table of Contents
What is the KillDisk (troj_killdisk.iub) ransomware?
The perpetrating program codenamed KillDisk has been around for at least two years. Its early recorded activity commenced in late 2015, when a mysterious cybercriminal group dubbed Telebots used it in tandem with the BlackEnergy malware to hit Ukrainian power infrastructure. It’s back then that researchers started associating the infection with Russian state-sponsored black hats. Later on, KillDisk was leveraged in attacks fired at industrial equipment in the United States and a few more high-profile incidents. The most recent incarnation of this culprit has been targeting Latin American firms from the finance sector. This particular variant has been catalogued as troj_killdisk.iub. For the record, its SHA256 hash is 8a81a1d0fae933862b51f63064069aa5af3854763f5edc29c997964de5e284e5.
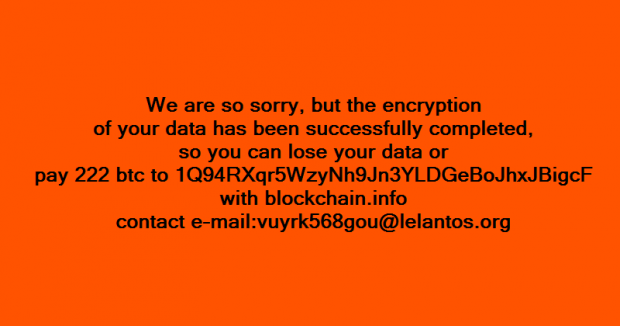
The modus operandi of this highly disruptive malware has gone through some evolution since its emergence. Whereas it originally pursued the objective of outright data wiping, it has come to imitate classic ransomware in order to add a ‘red herring’ component to the crooks’ routine. In other words, KillDisk still cripples the data of a contaminated entity – be it an organization, factory, bank or government body – but usually displays a ransom note to make it look like the adversaries are after money. Meanwhile, the threat actors seek to simply erase a target’s valuable records and harness some ransomware hallmarks as a smokescreen covering the tracks of their sabotage.
The troj_killdisk.iub iteration of the KillDisk pseudo ransomware is extremely stealthy when inside a compromised host. It is most likely to be deployed on a machine manually via sophisticated access abuse, such as RDP connection hacking or the use of software exploits. Then, the malicious code gets integrated into memory, wipes its files from local storage and renames itself to evade detection by commonplace security solutions. On the next phase, KillDisk overwrites a predefined number of Master Boot Record sectors and does the same to the first 2800 bytes of every file stored locally as well as on removable media. At this point, it skips some system-critical directories to ensure the computer keeps functioning. These include Windows, ProgramData, Program Files, System Volume Information and a few others. After a specified time interval, typically 15 minutes, the infection terminates four critical executables (csrss.exe, lsass.exe, wininit.exe and winlogon.exe), so the workstation will automatically reboot itself and won’t enter normal Windows interface any longer.
KillDisk in its current form is, obviously, a calamity to encounter. It sticks with scorched-earth tactics, so the plagued organization’s important records will most likely be erased beyond recovery. Again, its ransomware-like behavior is nothing but a distraction maneuver, so it’s strongly recommended to adopt proactive defense when it comes to avoiding this nasty malady. Data backups are still such a must.
KillDisk troj_killdisk.iub ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download KillDisk troj_killdisk.iub ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by KillDisk troj_killdisk.iub ransomware
Workaround 1: Use file recovery software
It’s important to know that the KillDisk troj_killdisk.iub ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether KillDisk troj_killdisk.iub ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓