.java ransomware decryptor: [decrypthelp@qq.com] Dharma virus removal
![.java ransomware decryptor: [decrypthelp@qq.com] Dharma virus removal](https://soft2secure.com/wp-content/uploads/remove-java-files-ransomware.png)
The ransomware lineage codenamed Dharma, or CrySiS, is one of the progenitors of the present-day landscape of file-encrypting viruses. It is one of the few that continue to be updated on a regular basis despite the overall decline in this type of online extortion recorded lately. The most recent variant speckles encrypted files with the .java extension.
Table of Contents
What is the .java files ransomware?
For disambiguation’s sake, it makes sense to mention from the get-go that the .java extension virus has nothing to do with the popular programming language that goes by the same name. This rogue resemblance is nothing but a whim of CrySiS/Dharma ransomware deployers who chose to use the word as the new extension being affixed to hostage files. Said family of blackmail malware keeps expanding rapidly, this evolution being accompanied by switching the external indicators of compromise. Victims have been reporting incidents where their data becomes inaccessible and assumes a weird look following a pattern like this: Filename.[original extension].id-[victim ID].{email address}.java. Some versions may have the email string enclosed in square brackets instead.
The CrySiS ransomware editions currently in rotation append the .[habibi.habibi3@aol.com].java, .[decrypthelp@qq.com].java, or {faremar@cock.li}.java extension to encrypted files (note the curly braces in the latter). Regardless of the final extension string, the other commonly reported email addresses include black.mirror@qq.com and chivas@aolonline.top. As of April 2018, the extortionists have released a few more .java ransomware variants that use the following contact email strings: bacon@oddwallps.com, pepsi666@protonmail.com, recoverys2018@cock.li, and decrypt.guarantee@aol.com. So, there appear to be multiple sub-iterations of this version that’s getting increasingly prolific.
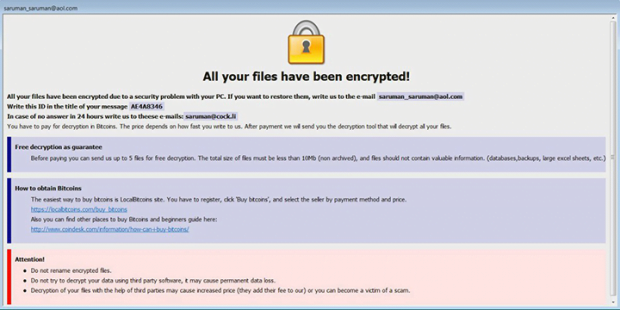
Another attribute of the .java ransomware is the rescue note that gives the victim an idea of what exactly has happened and how to get the data back. It may come in two variants. One of them named Info.hta gets configured to splash up without user action via a command invoked surreptitiously. Another one, FILES ENCRYPTED.txt, is dropped on the desktop so that the victim can open it when they deem appropriate.
In a nutshell, the contents of these ransom notes are quite prosaic: the user is supposed to shoot a message to the indicated email address for specific recovery instruction. The unique victim ID should be entered in the title of this message so that the crooks can work out which decryption key is a match for a particular case. The user has an option of sending up to five files for free decryption, on condition that those don’t contain important information and don’t exceed 10Mb in size. In response, the threat actors will send details on the amount to be paid and the Bitcoin address to submit the ransom. Its size is calculated individually and depends on the value of encrypted data and the number of machines infected. If it’s an enterprise network, the ransom will most likely be larger than for a home user.
The .java variant of CrySiS ransomware is distributed via compromised remote desktop services. In other words, the cybercriminals hack into computers by picking RDP access credentials. The methods for doing so may range from entering common passwords to brute-forcing them. One way or another, RDP connection should be protected reliably enough to thwart this vector of attack. In case this ransomware has made its way inside and there are numerous encrypted files with the .java extension, start with the cleanup and recovery techniques below.
.Java extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download .Java ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the extension and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by .Java extension
Workaround 1: Use file recovery software
It’s important to know that the .Java extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether .Java extension has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the extension itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓