Remove iGotYou ransomware and recover .iGotYou virus files
There are blackmail viruses that stand out from the rest – ones like the professionally tailored and highly prevalent Cerber, Locky or CrySiS. On the other hand, there are mainstream ransom Trojans that cannot boast massive distribution but do cause a great deal of problems to those infected. The new iGotYou ransomware undoubtedly falls into the latter cluster.
Table of Contents
What is the iGotYou ransomware?
When originally discovered on November 22, 2017, the iGotYou crypto threat was in a sort of evaluation state and didn’t encrypt anything except the contents of the Test folder on its author’s C drive. Security analysts have gotten resourceful enough to spot malware in pre-propagation period, which is good news. The bad news is, things have changed ever since as the culprit has been seen in the wild and victims get their valuable files locked down in multiple different locations. These include hard disk partitions, removable drives and network drives. When this perpetrating program affects a file, it stains it with the .iGotYou extension, hence the name of the baddie.
The main vector of distribution leveraged by the maker of iGotYou is malspam. The anatomy of this mechanism is as follows: an unsuspecting user receives an email containing some eye-catching information, such as a subject that goes, “Invoice” or “Your scanned fax copy”. The harmful component of this email is the attachment, which tends to be a Word document with toxic macros on board, or an obfuscated JS (JavaScript) object. Once double-clicked, this entity surreptitiously triggers the infection chain by downloading the rest of the malign components onto the recipient’s machine.
When executed and running, the iGotYou ransomware scans the host for widespread formats of data, such as .doc(x), .xls(x), .bmp, .jpg, .jpeg, .mov, .avi and many others. Every matching item detected in the course of this scouring is subject to unsanctioned processing with a cipher. This particular Trojan most likely employs AES (Advanced Encryption Standard), which isn’t the strongest cryptosystem across the board but it makes files inaccessible for good. The prerequisite for decryption is the availability of the secret AES key, which is kept by the threat actor running the extortion campaign.
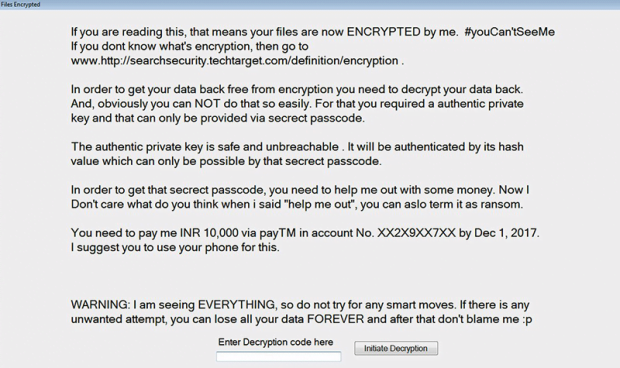
To provide the prey with instructions on how to get this code and regain access to the hostage data, the offending program drops a ransom notification named “Files Encrypted”. It says, “If you are reading this, that means your files are now ENCRYPTED by me. #youCan’tSeeMe. In order to get your data back free from encryption you need to decrypt your data back.” The note instructs the plagued user to pay INR (Indian Rupees) 10,000 (about $155) via Paytm, a popular Indian electronic payment system in. This hallmark happens to be a distinguishing trait of the iGotYou ransomware, because most blackmail infections demand cryptocurrency like Bitcoin.
It’s hard to state for a fact at this point whether it’s 100% effective to use forensic recovery methods for reinstating .iGotYou extension files – the study of this infection is still in progress. However, the tips listed below are certainly worthwhile as a starting point. Be advised that before trying to get the data back this way, it’s a must to get rid of the malicious code proper.
iGotYou extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download iGotYou ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the extension and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by iGotYou extension
Workaround 1: Use file recovery software
It’s important to know that the iGotYou extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether iGotYou extension has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the extension itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓