Hermes 2.1 ransomware: how to recover .HRM files

The current state of the ransomware underground is versatile enough to spawn crypto infections whose objectives are blurred. The classic file-encrypting Trojans pursue the sole goal of ripping off their victims by making them pay ransoms for data recovery. Culprits like the Hermes 2.1 ransomware, though, are nastier than that.
Table of Contents
What is the Hermes 2.1 ransomware?
There is an intricate story behind this blackmail malware sample. Its original variant was discovered in February 2017 and hardly made it to wide distribution over the following months. This hiatus was temporary. The perpetrating program showed its ugly fangs big time in mid-October last gyear. It was used in a high-profile bank heist targeting the Taiwan¬-based Far Eastern International Bank. The threat actors, who are believed to be from North Korea, leveraged the ransomware as a red herring, that is, to distract the target from the theft of funds. The Hermes 2.1 edition currently in rotation, though, appears to operate as garden-variety ransomware.
Hermes 2.1 ransomware is distributed mainly via malspam carrying booby-trapped attachments in the form of Microsoft Word files with macros or ZIP archives that contain malicious JS (JavaScript) objects. Another likely contamination vector engages exploit kits, where users get hit surreptitiously after visiting a compromised website. One way or another, the attack workflow is equally rapid and has adverse consequences. The Trojan invokes a number of commands to maintain persistence on the host and evade the regular antivirus detection mechanisms. Then, it scans the hard drive and network shares for potentially important data.
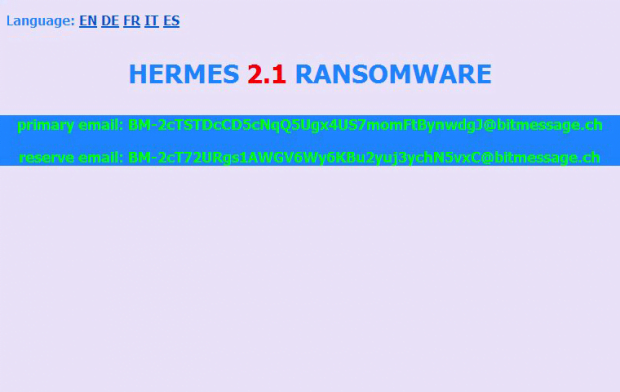
Every single file spotted in the course of this scan is subject to encryption. Hermes 2.1 ransomware utilizes a fusion of asymmetric RSA cipher and CryptGenRandom function that’s part of the Microsoft CryptoAPI. As a result, the victim can no longer work with their files – neither opening nor editing them is possible. The pest also appends the .HRM extension to every encrypted object while keeping the original filenames unaltered. To instruct the victim regarding data recovery, it drops a ransom note named DECRYPT_INFORMATION.html. According to this how-to, the infected user is supposed to send a message to a specified email address, attaching a file named UNIQUE_ID_DO_NOT_REMOVE to it.
Just like in the average ransomware scenario, Hermes 2.1 demands a certain amount of Bitcoin for the private RSA key. The size ranges from 0.1 to 1 Bitcoin and depends on whether it’s a home PC or a computer network that got hit. It is strongly recommended to abstain from submitting any funds to the crooks, because it is likely to end up being a waste of money. Instead, try the steps below to see whether alternative techniques can do the trick.
Hermes 2.1 extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Hermes 2.1 ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the extension and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Hermes 2.1 extension
Workaround 1: Use file recovery software
It’s important to know that the Hermes 2.1 extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Hermes 2.1 extension has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the extension itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓