Gryphon Decrypter: ransomware removal and .gryphon files recovery
Cybercriminals are well motivated as long as their misdemeanor brings them a pretty penny. This seems to be the case with the new Gryphon ransomware. Having landed on a targeted host, it denies accessibility of the victim’s important files, appends them with the .gryphon extension and holds them for ransom. Learn what lineage this sample represents, how to distinguish it from others, and how to restore encrypted files.
Table of Contents
What is the Gryphon ransomware?
Data-encoding virus called Gryphon ransomware is part of the notorious BTCWare family. As opposed to earlier iterations of this strand that stuck with exploitation of remote desktop services to infect computers, this one is propagating via malspam. The ongoing distribution campaign is referred to as “Blank Slate” because the booby-trapped emails don’t contain any text in their subject field and body. Recipients who end up unpacking the attached ZIP file out of curiosity or for whatever other reason run the risk of unknowingly launching an embedded JS script, which completes the attack chain.
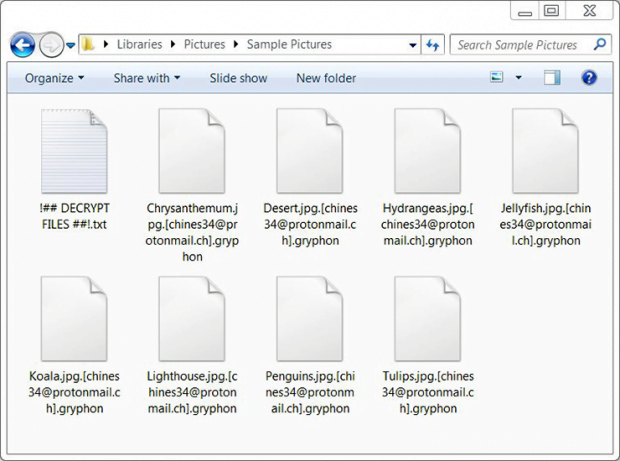
Once malicious code deployment has been performed, the Gryphon virus scans the contaminated machine for data that’s potentially of the highest value to the victim. It goes equipped with a list of file extensions to target along the way. To add insult to injury, the ransomware looks inside network drives and removable media, in addition to local drive volumes. Every matching entry that’s detected during this checkup is then encrypted with asymmetric public-key RSA cryptosystem. Not only do those files become inaccessible, but they also change externally. The original filename and extension will be appended with the threat actor’s email address and the .gryphon string at the end. For instance, an image named Desert.jpg will transform into an entity that looks like this: Desert.jpg.[chines34@protonmail.ch].gryphon. Other reported extensions that the infection affixes to filenames include .[decr@cock.li].gryphon and .[bravobravo@cock.li].gryphon.
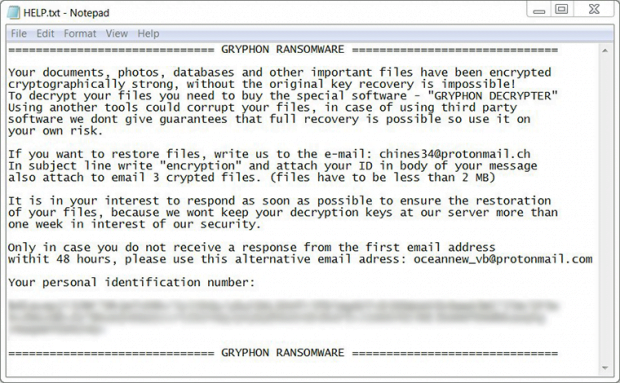
Additionally, the offending code creates what’s called ransom notes. These are documents containing the essentials of data decryption imposed by the malefactors. Such files usually show up on one’s desktop and inside all affected directories. In the case of the Gryphon ransomware, these manuals can be named HELP.txt, Help.inf, Info.txt, or !## DECRYPT MY FILES ##!.txt. The message in these how-to’s is as follows, “Your documents, photos, databases and other important files have been encrypted cryptographically strong, without the original key recovery is impossible! To decrypt your files you need to buy the special software – GRYPHON DECRYPTER.”
In other words, the crooks upsell their decryption tool. The price for it is somewhere around 0.5 Bitcoin, or about $1,700. With that said, the attackers offer victims the option of restoring up to three files without any payment as long as they are less than 2 MB in size. It has not been confirmed at this point whether this proposal is real, though. There is also a time limit to pay up, which is one week. After it expires, the decryption keys will be allegedly wiped from the secret server. Instead of going the ransom way, Gryphon ransomware victims are strongly recommended to try all the other possible options first. Get more details in the sections below.
Gryphon ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Gryphon ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Gryphon ransomware
Workaround 1: Use file recovery software
It’s important to know that the Gryphon ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Gryphon ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓