Remove fanli90.cn redirect virus in Chrome, Firefox and IE
It’s not too uncommon to discover these days that a web browser’s homepage starts defaulting to a site that’s not the user’s choice. In pursuit of easy Internet traffic monetization and malvertising, some cybercrime groups leverage malicious code called browser hijackers. These intrusive applets infect computers and adjust the functioning of installed browsers to specific nefarious goals. The infection causing the fanli90.cn website to pop up instead of one’s preferred start page is both commonplace and offbeat at the same time.
Table of Contents
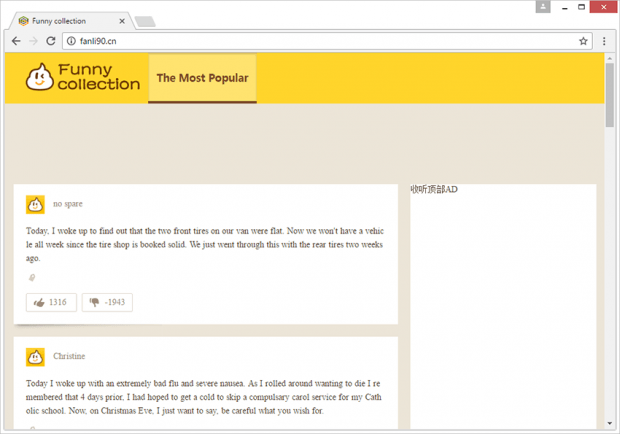
What is fanli90.cn?
Titled “Funny collection”, the site under scrutiny looks like an innocuous blog with nothing clearly harmful under the hood. However, the entirety of adverse activity going on behind the scenes of this rather boring online resource poses a serious security concern that’s no fun at all. The fact is, Fanli90.cn also denotes an adware strain that aggressively modifies the configuration of web browsers detected on a plagued machine. Specifically, it tweaks the settings of the corresponding shortcuts so that the victim will keep visiting the wrong site every time they launch Google Chrome, Mozilla Firefox, Internet Explorer or other browser installed. The hijacker appends the original Target value of shortcuts with the rogue URL, thus defining a new action triggered when the icon are double-clicked.
To top it off, the fanli90.cn virus also adds a new intrusive extension to Chrome. It’s called Easychrome. The objective of this add-on is to insert sponsored items into the content of visited websites. These may include graphical comparison shopping sections, popup ads, in-text links and interstitial advertisements. Not only do the redundant objects cram up regular web pages, but they also tend to have a slowdown effect that considerably increases site loading time. Furthermore, the unwanted extension monitors the victim’s web surfing activity in order to display sponsored information that matches their interests and lifestyle. The promotion of this pseudo helper object makes the hijacker double trouble.
The uniqueness of the fanli90.cn infection revolves around the fact that it operates without installing a separate application on a computer system. Instead, it achieves the shortcut-twisting goal by executing a specific VBScript command. This isn’t the general tactic leveraged by adware. As a result, some antimalware programs may raise red flags on the affected shortcuts but won’t detect the actual perpetrating code, which is something that complicates troubleshooting.
While functioning in a non-standard way, the hijacker propagates just like the majority of its counterparts do. Its payload lurks under freeware installers available on various download hubs, including popular ones. The trick is that the default, or recommended, preset of the booby-trapped installation clients will serve up the malicious code alongside harmless apps, such as media players or movie downloaders. It’s therefore always a good idea to explore the structure of a freeware setup by selecting the custom option. This way, users can opt out of potentially unwanted entities like fanli90.cn and its concomitant adware. In case this malady is already on board a system, there is no need to panic – just stick to the steps below and bid farewell to the nuisance.
Fanli90.cn adware automatic removal
The extermination of Fanli90.cn hijacker can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the redirect removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the adware is gone for good.
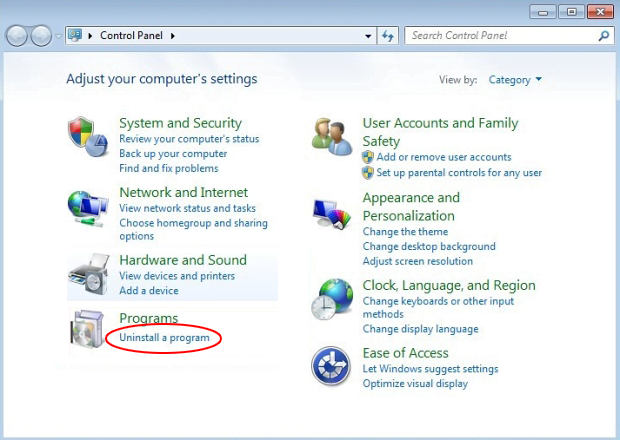
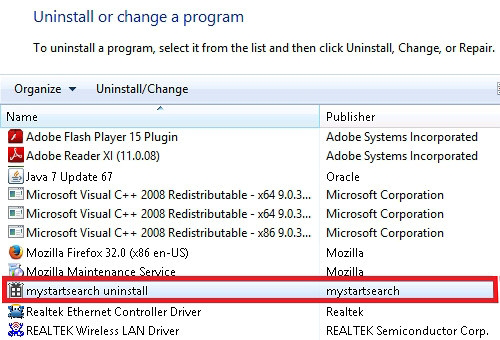
Remove Fanli90.cn adware using Control Panel
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Fanli90.cn adware removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
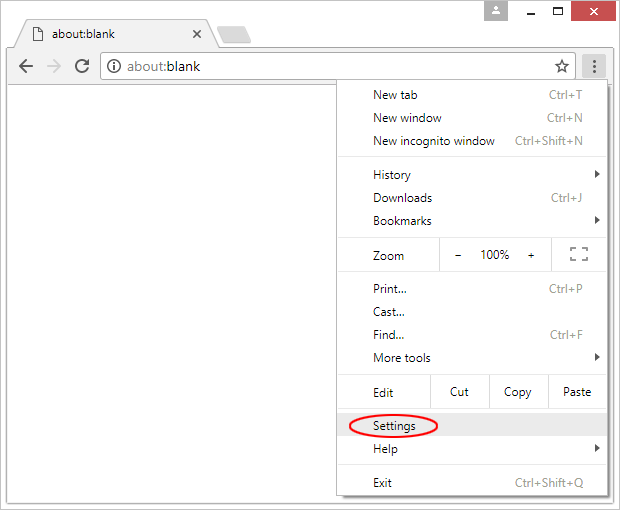
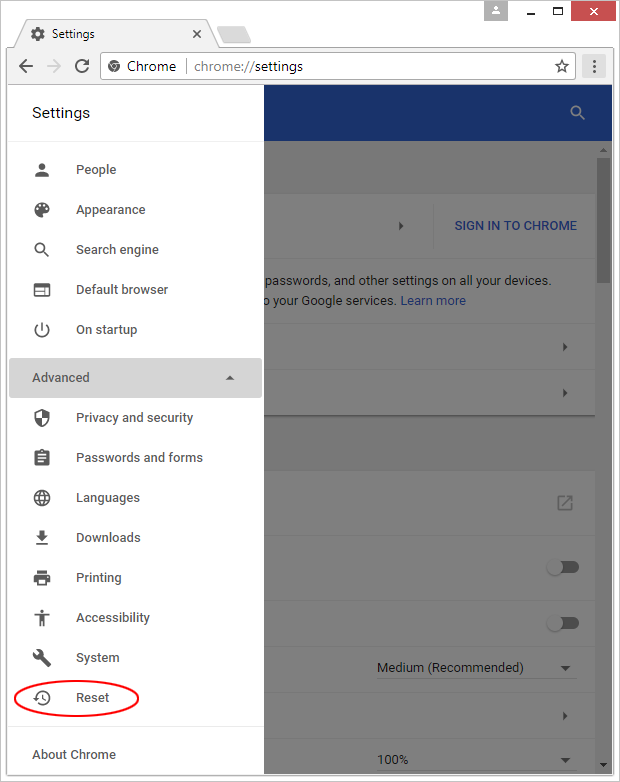
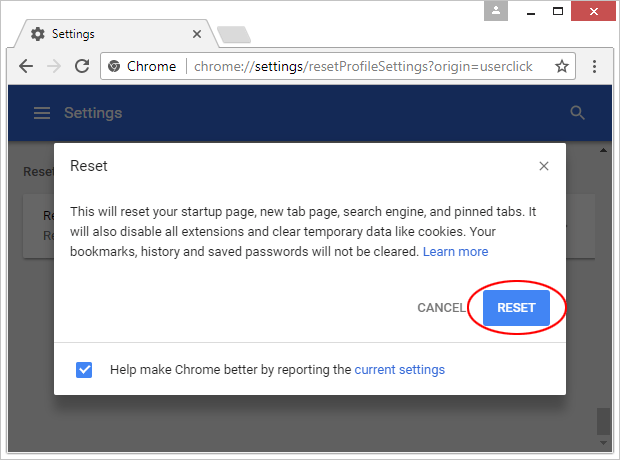
Reset Google Chrome
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

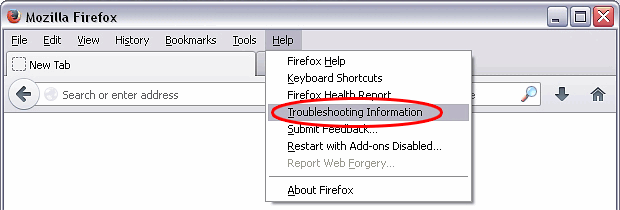
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

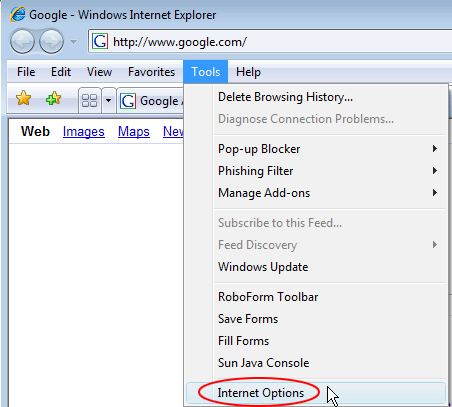
Reset Internet Explorer
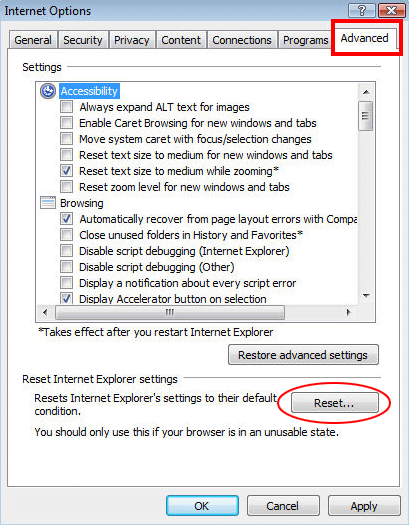
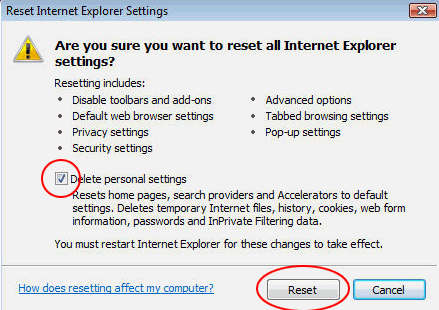
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether Fanli90.cn adware has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this hijacker are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓