Once Again, Do Not Use Public Wi-Fi

Some of you may find the information below obvious and prosaic, but while talking to colleagues in the smoking room one day I realized that many people, including those who are proficient in IT, never took it seriously, not to mention the ones who aren’t tech-savvy.
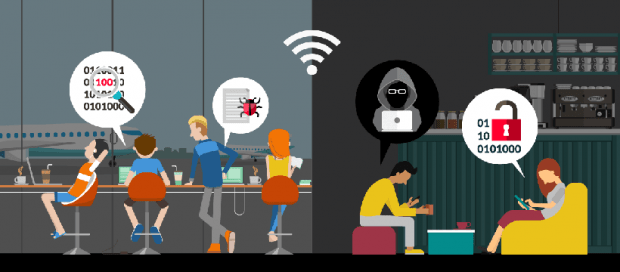
When the question comes up about the downsides of public Wi-Fi in the transport, cafes, hotels, etc., the most common answer is either about encryption that’s completely missing or about the use of the same encryption key for all connections. Someone may reasonably say in response that nearly all websites and services use HTTPS nowadays, therefore a criminal who’s tapping the network cannot obtain your passwords and sensitive information.
Security-minded or sensibly paranoid people use numerous VPN services when going online from public networks, thereby creating an extra layer of protection. You can also select the one to your liking from this list created by Bestvpnrating.
According to the legislation of some countries, user authorization is the main prerequisite to free WiFi access. When connecting to a public wireless network, a user must obligatorily verify their identity and go through device identification. When you are connecting to a public Wi-Fi hotspot for the first time, you are automatically redirected to an authorization page. The authorization can be done in several ways:
- By entering a mobile phone number to receive a confirmation code via SMS or a voice call. In many countries, subscribers need to provide their identity information to buy prepaid SIM cards.
- Some ISPs (Internet service providers) allow customers to authenticate with their public Wi-Fi networks by entering the same username-password combo they use for home Internet. It means these ISPs know who is connecting because they already have contractual relationship with these people and know their identity details.
Every time the authorization takes place, the service provider logs your device’s MAC address along with a certain identifier that clearly points to you (phone number, contract number, etc.). The motivation is to make sure you don’t go through the whole authorization procedure all over again the next time you connect to the same wireless network – the provider’s router will recognize your phone, tablet or laptop by its MAC address and it will automatically apply the appropriate access rules. Most of the time, the MAC address is the only property the ISP uses to verify your identity.
Table of Contents
A real-world scenario
You, a law-abiding person, have come to some public place, such as a cafe or subway, performed authorization with the public Wi-Fi network using your phone number or any other identifier, spent some time surfing the web, then disconnected and left that place.
This co-occurred with someone not so law-abiding visiting the same place. That person had a commonplace laptop equipped with a garden-variety Wi-Fi adapter that could work in monitor mode that also had utilities from the Aircrack-ng package installed on it. The bad guy was inconspicuously tapping the wireless network to record the MAC addresses of devices that went online, exchanged traffic with the access point, and then disconnected from it.
After you left the place with that wireless network coverage, the culprit manually replaced their Wi-Fi adapter’s MAC address with the MAC address of your device, connected to the network, the equipment identified him as you and allowed the Internet session without any authorization.
It’s worth mentioning that these things aren’t necessarily done with evil intentions. Some people (all characters and events described here are fictitious) may do it to avoid ads when browsing in a subway Wi-Fi network (by finding a MAC address of a person who subscribed to premium ad-free service). Some other people may want to use your address for online torrenting.
Having successfully logged in with your credentials, the bad guy may do illegal things as well. That’s where the “fun” part begins.
In compliance with the local laws or at their own discretion, some ISPs keep authorization logs for several months. In case law enforcement representatives submit an official inquiry to the provider whose network was used to commit an online crime, the logs will point to you rather than the felon because the misdemeanor was done from a device with your MAC address.
Ideally, the whole predicament will fall apart at the pre-investigation check stage. In a better-case scenario, you will have to waste your time and take efforts to prove that you have nothing to do with the crime. You may need to engage experts who will affirm that a MAC address cannot be considered an ultimate identifier of a device and specific user. You will probably also have to collect witness statements and surveillance camera videos (unless they expire and get erased) that confirm you were no longer there when the crime was committed. Also, you will have to set your hopes on the judge not dismissing your petitions about adding all that evidence to the case.
How can you avoid this?
Unfortunately, you can’t. Everything comes down to the imperfections of authorization and authentication methods leveraged by service providers, as well as the peculiarities of the legal and judicial systems. There are no technical mechanisms to prevent such situations from affecting regular users at this point (we’re not considering the situation with SIM cards registered by someone else). The takeaway is obvious: do not use public Wi-Fi networks.
It’s also noteworthy that the necessity to exercise caution isn’t restricted to public Wi-Fi only. Wireless routers used by most people at home utilize the WPA2-PSK encryption protocol, which is known to be susceptible to hacking through dictionary attacks. If you use an easy-to-guess password (although even a strong one won’t do the trick in the future as computation power grows and becomes cheaper), someone else may be able to connect to your home Wi-Fi and go online as if they were you, the owner of the router. This issue can be addressed by technical means. For example, you can configure the equipment to only access the VPN server over WiFi or use WPA-802.1X – in either case, the hardware must support the option. Very few users bother doing it, though.
Posted in: KnowledgeBase
Leave a Comment (0) ↓