Delta email scam – beware of fake emails from delta@performanceair.com
There aren’t many domains as sensitive for the average person as the services of airlines. People naturally want to stay on top of flight schedules as well as the status of booking transactions and payments. Online fraudsters couldn’t have possibly walked by this segment of economy. A recent scam, for instance, distributes malware by duping users into clicking on a link in emails from delta@performanceair.com.
Table of Contents
What is the Delta email scam (delta@performanceair.com)?
Delta email scam revolves around fake emails impersonating Delta Airlines, Inc., one of the largest airlines in the United States. The cybercriminals at the helm of this hoax attempt to entice computer users into unknowingly downloading malicious software. The booby-trapped messages from delta@performanceair.com are camouflaged as order approvals. To view and print an alleged flight ticket, recipients are instructed to click on a link that triggers a drive-by malware download process. Obviously, most users who receive such emails didn’t actually make any orders of that sort, which is one of the main giveaways in this whole con. However, such messages do evoke a great deal of curiosity regardless, so lots of people end up following the trojanized link and get badly infected.
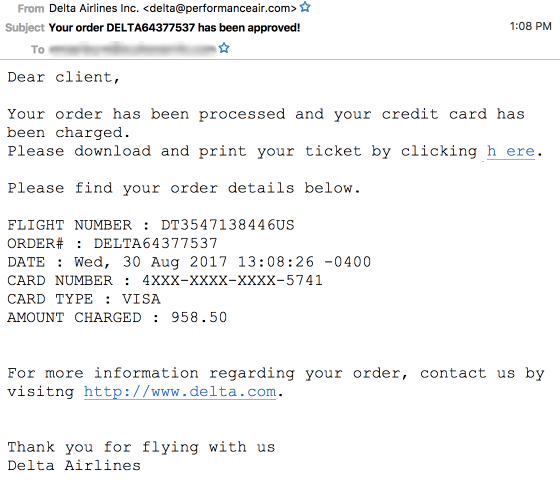
The sender displayed in the corresponding field of these messages is purportedly Delta Airlines Inc., but the address raises yet another red flag. Genuine notifications from this company will contain the ‘delta.com’ string for the domain, not performanceair.com. Unfortunately, users may be unaware of this or simply fail to pay attention. The subject of these counterfeit emails is in the following format, “Your order DELTA[random_digits] has been approved!” The message body goes,
Dear client,
Your order has been processed and your credit card has been charged. Please download and print your ticket by clicking here. Please find your order details below.
For greater persuasiveness, the email also provides an alleged flight number, order number, date, card number, card type, and amount charged. The gist of this hoax, though, boils down to the word ‘here’ that includes a hyperlink leading to one of the following phishing URLs: ourrealtyguy(dot)org, ourrealtyguy(dot)info, ourrealtyguy(dot).us, package2china(dot)com, or myhearthstonehomes(dot)org, all appended with ‘i.php?d=’ string. Once any web page from this list is visited, it drops a malicious Microsoft Word file onto the computer. The document, in its turn, injects a virus downloader known as Hancitor. This toxic entity reaches out to a C2 server and continues the contamination chain by additionally promoting several Trojans into the system, including Pony, EvilPony, and ZLoader.
It goes without saying that whoever receives an email sent from delta@performanceair.com shouldn’t click anything in it, otherwise a severe malware incursion is inevitable. If you have done so already, be sure to spot and remove the associated infections.
Delta email automatic removal
The extermination of Delta fake can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the scam removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the email is gone for good.
Posted in: KnowledgeBase
Leave a Comment (0) ↓