Remove default-search.net virus in Chrome, Firefox and Explorer

Assigning custom Internet browsing settings is supposed to be the prerogative of every computer user. This is the main constituent of web browsers’ flexibility that’s so much appreciated these days. There are malicious applications, though, designed to make all the benefits of this feature go down the drain. The adware called Default-Search is one of them. Keep reading to learn why.
Table of Contents
What is the default-search.net virus?
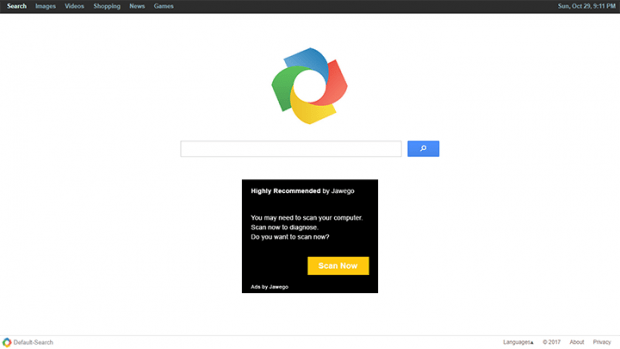
Default-search.net is a domain name tied to the shenanigans of a PUP (Potentially Unwanted Program) called Default-Search. The page itself appears to be harmless when visited, and that’s actually true. What makes it shady, though, is that it is part of a large-scale wave of browser hijacking that has hit and continues to affect numerous users around the globe. The negative upshot of the attack is all about redirects of a victim’s web traffic to the site in question. The prey’s preferred search engine, homepage and new tab page values get skewed and start defaulting to the unwelcome website. Because the infection is cross-browser, there is little chance that the plagued user’s online navigation software remains intact. It zeroes in on Chrome, Firefox, Internet Explorer, and there have also been reports about Microsoft Edge and Opera acting up due to this interference.
At the time of this writing, default-search.net invokes another instance of rerouting when a user enters an arbitrary query in its search box. The traffic goes on to Yahoo!. This is probably the threat actors’ attempt to make it look like their nefarious service is legit and goes equipped with real keyword lookup functionality, which it certainly doesn’t. The landing page proper contains a large ad or several advertisements underneath the search field. These items are powered by an ecommerce provider, such as Jawego, and serve the purpose of monetizing user hits from the get-go. It’s noteworthy that this content is targeted, which indicates that the virus intelligently determines the victim’s interests, likes and habits by spying on their online activity. Indeed, preliminary analysis reveals that the perpetrating application assumes privileges allowing it to access users’ browsing history, searches made, bookmarked pages and the like. To top it off, the PUP does it without asking for permission in any form.
The default-search.net virus gets deposited onto computers by means of a trick as old as the freeware distribution industry itself. It’s called bundling. Here’s how it works. Some software developers do not charge people for using their utilities, but there is still quite a bit of financial reward involved in this process. To get the bang for their buck, these enthusiasts resort to the services of software download repositories. The latter, in their turn, cook up installation clients where the core freeware is only part of the setup. The inclusion of additional products in the default mode of these setup wizards is the vector used by Default-Search adware authors and fellow-crooks to disseminate their pests beyond clear authorization on customers’ end. The takeaway is to treat free application downloads with caution and refrain from opting for the recommended installation option. In case the infection is on board already and wreaks havoc with web browsers, go ahead and follow the procedure below to resolve the problem.
Default-search.net adware automatic removal
The extermination of Default-search.net hijacker can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Default-search.net remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the adware removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the adware is gone for good.
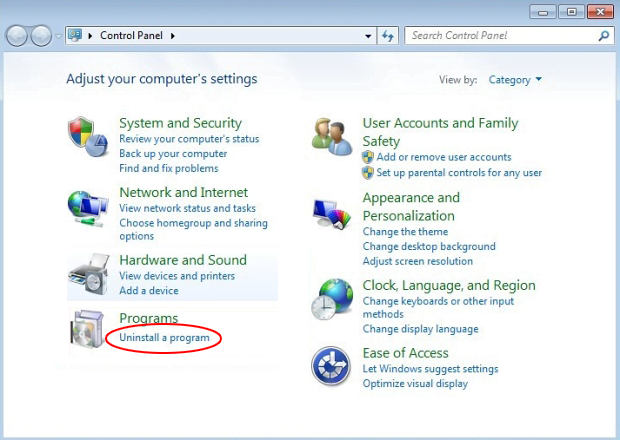
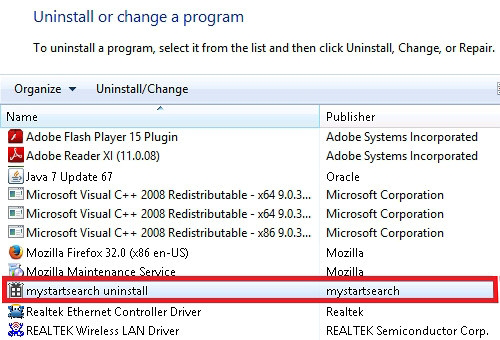
Remove Default-search.net adware using Control Panel
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Default-search.net adware removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
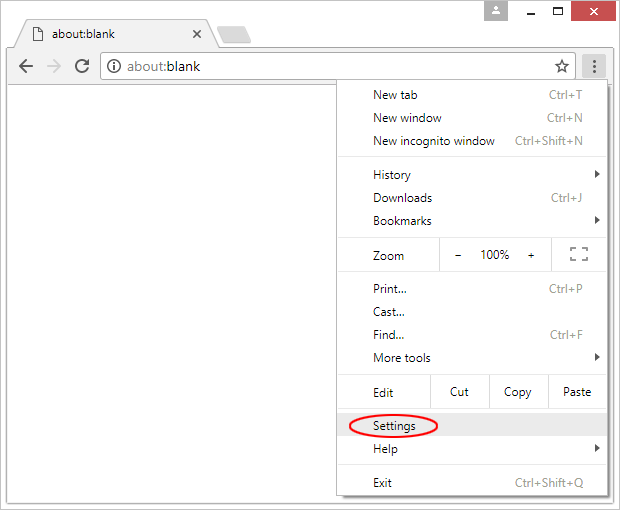
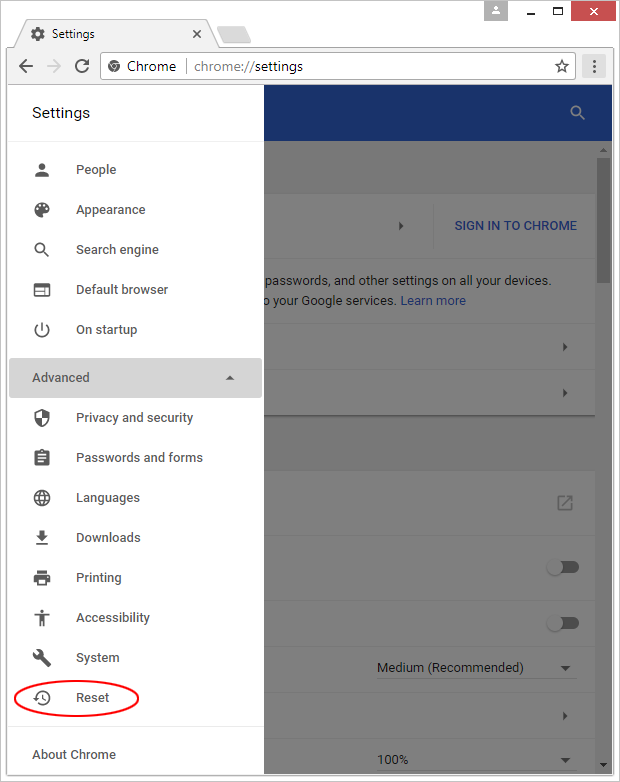
Reset Google Chrome
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

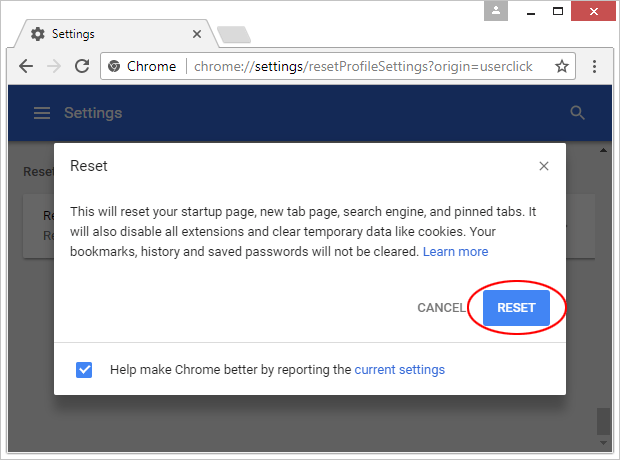
- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

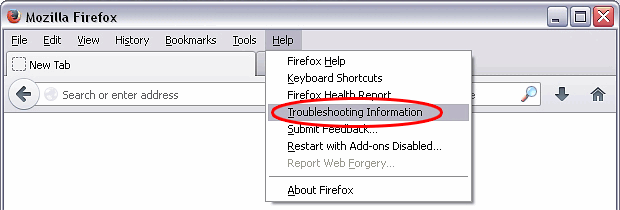
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

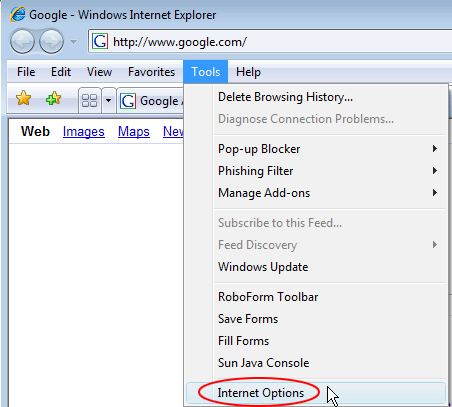
Reset Internet Explorer
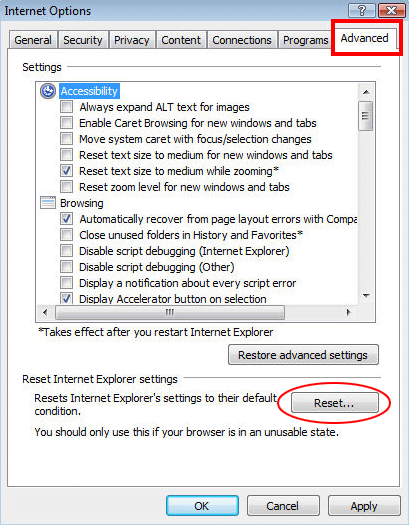
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

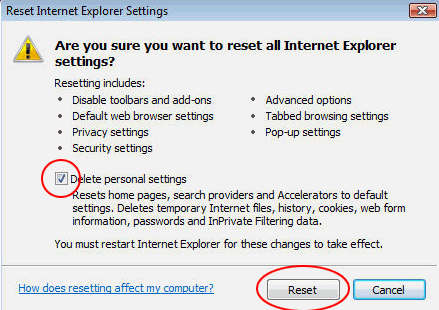
- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether Default-search.net adware has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this hijacker are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓