CryPy ransomware decryptor and removal
Python-based ransomware is not a new phenomenon in the online extortion environment, but it hadn’t been nearly as well-orchestrated as it has become with the emergence of the CryPy baddie. This crypto threat is proficient at evading antiviruses and leverages an extraordinarily hard-to-tackle encryption principle. The main hurdle to handling these attacks is that the infection enciphers every file with a standalone key.
Table of Contents
What is CryPy ransomware?
The reason why this ransomware is getting more red flags raised than the overwhelming majority of its extortion-driven counterparts revolves around its encryption approach. Once it obtains a list of a victim’s personal files through an obfuscated scan of the hard disk and network shares, each one of these entries gets cryptographically scrambled with an AES unique key. This peculiarity means that successful recovery from the compromise requires the retrieval of all private keys, the number of which may be in the thousands. There is hardly any user or organization with sufficient computation resources to solve this immensely complex puzzle. To top it off, CryPy attempts to erase all shadow copies of an infected user’s files, disabling this workaround of data restoration for good. It also modifies Windows registry to make sure its processes – encryptor.py and boot_common.py – are executed upon operating system boot-up.
According to security researchers’ analysis, CryPy uses a hacked web server over in Israel as its Command and Control unit. Interestingly enough, this isn’t the first time computer threat actors have parasitized the exact same server, which is reportedly also being used as a springboard in a large-scale phishing campaign. A vulnerability in the Magento Content Management System was the original entry point for the compromise. This incident should, obviously, become another wakeup call for webmasters, who should keep their CMS components up to date at all times.
The operation of the CryPy ransomware on a contaminated computer is barely conspicuous on the early stage of the attack. The prepping phase includes the above-mentioned registry changes and a behind-the-scenes scan for personal data. The Trojan has a hard-coded list of about 200 file extensions that it uses to identify the information that matters the most to a victim. Aside from local drive volumes, it also scours removable media if any, as well as every network repository that the user is authorized to access. Again, CryPy request an individual crypto key for every detected object.
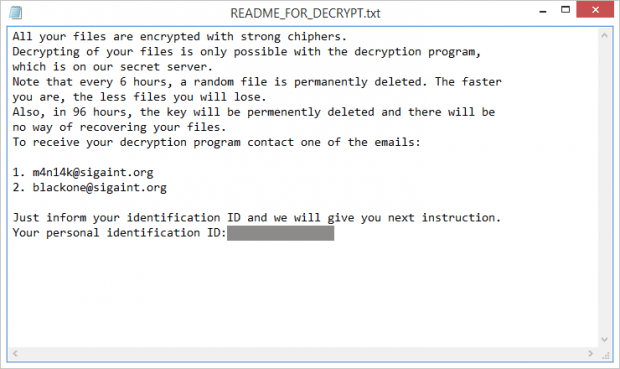
To provide the user with a roadmap for decryption, the pest adds a Notepad document named README_FOR_DECRYPT.txt on the desktop. It also configures the OS startup routine so that this file is opened automatically. The ransom note says, “All your files are encrypted with strong chiphers [sic].” By the way, the spelling quality leaves a lot to be desired, which may indicate that the threat actor is not a native English speaker.
CryPy authors instruct victims to reach them at m4n14k@sigaint.org or blackone@sigaint.org for recovery steps. They will send information on the ransom size and Bitcoin wallet address in response. This isn’t the most sophisticated way to interact with infected users imaginable, but it apparently works for the crooks. If confronted with this ransomware, though, it won’t hurt to try alternative remediation methods.
CryPy ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download CryPy ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by CryPy ransomware
Workaround 1: Use file recovery software
It’s important to know that the CryPy ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether CryPy ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓