Remove CryptoWall 3.0 ransomware: CryptoWall 3.0 removal and decrypter

To those who are keeping track of malware news and those who fell victim to the recently released CryptoWall 3.0 scam, this post is the right place on the Internet to visit. The article includes exhausting details about this infection, its background, features of the latest variant, and certainly a couple of ways to undo the harm it calls forth as well as to get rid of the malicious program proper.
Both security gurus and PC users had a sigh of relief as the spreading of CryptoWall haulted in late fall 2014. The damage it had caused to thousands of people at that moment was immense because of the realm it had been targeting – personal files. What this nasty threat does is it encrypts the victim’s personal data and extorts a ransom afterwards. The propitious suspension of this ransomware’s operation, unfortunately, didn’t turn out to be long-lasting. Binaries of an updated version called CryptoWall 3.0 started to surface here and there in mid-January 2015, so it’s just about time to dissect the new sample from different angles and see how its impact can be addressed.
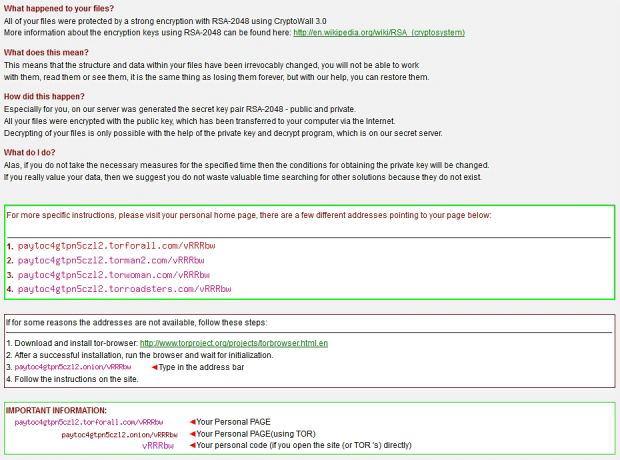
As per technical characteristics, a lot of things have remained basically unmodified. The main focus is on encrypting one’s files using the same standard, RSA-2048. In plain language, this means that the information is encoded with very strong crypto, where two main things are required for decryption: the public key and the private key. Whereas the former component stays on the compromised machine in this case, the latter it kept in a remote location. Since addressing the problem here is a matter of the availability of both prerequisites, the creators of this ransomware basically sell you the private key and the program that automatically runs the decryption process. The cost of this deal is $500 – to be more precise, the equivalent of this amount in Bitcoins. Why Bitcoins? Experts believe it’s because of more anonymity during payment transactions, so it’s the criminals’ hedge against getting tracked down.
With much similarity in place, there are some changes in CryptoWall 3.0 as compared to the predecessor. One of the realms is distribution, which underwent drastic refining. The virus now adopts exploit kits-related tricks, which is a much harder-to-avoid technique than the formerly employed embedding of exploits into the dropper object. So software vulnerabilities are the main intrusion channel. Another upgrade component relates to communication with the ransomware’s server, which now uses a more diversified set of Web-to-Tor gateways. And lastly, speaking of modifications, the ransom deadline has increased to 7 days.
To sum it up and add a few more facts, CryptoWall 3.0 attacks computers stealthily; it scans the system to find all files that can be considered personal rather than system-level; it encrypts the detected files with RSA-2048 algorithm and then displays a PNG file named HELP_DECRYPT with further instructions and links to Tor pages tailored for data and payment processing. The 500 USD ransom is to be paid within 168 hours.
The fix should be viewed in two contexts: removing the ransomware and recovering the files it encrypted. Other than submitting the ransom, there is unfortunately no seamless and completely efficient method to restore the data, but some techniques, which are covered below, can be fairly helpful under certain circumstances that vary from case to case.
Table of Contents
CryptoWall 3.0 ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download CryptoWall 3.0 ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by CryptoWall 3.0 ransomware
Workaround 1: Use file recovery software
It’s important to know that the CryptoWall 3.0 ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether CryptoWall 3.0 ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓