CryptoWall virus removal: how to decrypt Cryptowall 2.0 encrypted files

In this tutorial you will be advised on the methods to treat the CryptoWall ransomware which encrypts personal user files on the compromised computer. Since this isn’t a run-of-the-mill infection, a complex procedure and caution are required for exterminating it and trying to not lose the data that it takes hostage. A full technical profile of this virus as well as applicable file recovery tips are covered here in detail.
The advancement of cybercrime schemes has been reflected in the emergence of highly sophisticated samples of malicious software in the past couple of years. Perhaps the most disturbing wakeup call has been made by the extraordinarily aggressive programs referred to as ‘ransomware’. There exist two basic types of these computer threats. The first group is screen lockers, intrusive applications that make the operating system inaccessible and extort a payment for getting the problem fixed. The other category deploys the encryption of victims’ personal files and provides decryption ability only after a ransom is paid. The entity known as CryptoWall represents the latter cluster. It was first detected in late spring 2014 and it has since been updated to CryptoWall 2.0, the new version getting a refined ransom payment algorithm and enhanced data restore prevention.
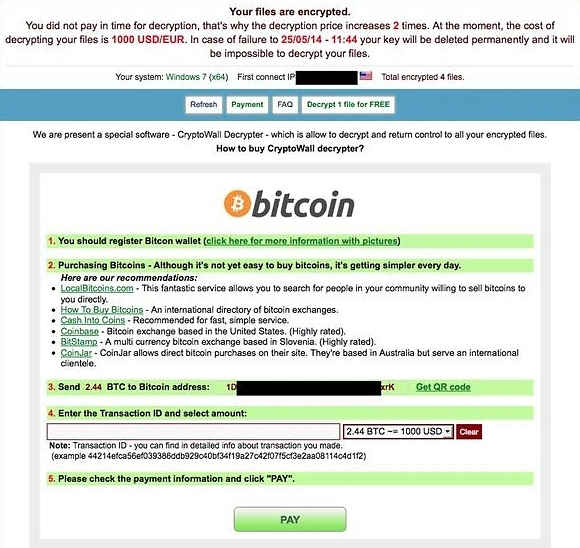
The ransomware in question spreads with email attachments disguised as PDF files inside a ZIP archive. As soon as these objects are opened, a drive-by download gets executed. This leads to the installation of the malware into Temp or AppData directories. This is a background process, so in most cases users find out they have been infected only after a ransom notification pops up. What CryptoWall does initially is it scans all drives on the compromised machine for files such as documents, images, presentations, videos and the like. It then encrypts these items with RSA-2048 algorithm, which makes the data unavailable without the private key and the special tool called CryptoWall Decrypter. This ‘service’ is costly, amounting to the Bitcoin equivalent of 500 USD (750 USD with the new version). In case the ransom is not paid within a specified time span, the fee doubles. Here is what the message says:
“Your files are encrypted. To get the key to decrypt files you have to pay 500 USD/EUR. If payment is not made before <time and date specified> the cost of decrypting files will increase 2 times and will be 1000 USD/EUR”
All communication with the bad guys’ command and control server are established via Tor browser, which makes it hard for the law enforcement to track them down. For CryptoWall 2.0, there have appeared dedicated Tor gateways currently hosted at pay2tor.com, tor2pay.com, tor4pay.com and pay4tor.com. Furthermore, every infected user is assigned a unique Bitcoin address so that the ones who paid the ransom don’t hand over the transaction details to others. Plus, the updated build of the malware employs erasure of the original files beyond recovery.
It appears that the fraudsters’ practices are secured in every way you could think of. The irony of the matter is that CryptoWall does not pose particular difficulty in terms of removal – an efficient security suite can do the job smoothly enough. The main problem, though, is how the encrypted data can be restored. At this point, there doesn’t exist a 100% reliable method for this other than paying the ransom and getting the decryption utility. However, there are several workarounds that might well do the trick and get you the files back. The instructions provided below highlight both the ways to remove CryptoWall from the affected PC and file restore tips that may help you out.
Table of Contents
CryptoWall ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download CryptoWall ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by CryptoWall ransomware
Workaround 1: Use file recovery software
It’s important to know that the CryptoWall ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether CryptoWall ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓