Decrypt CryptorBit ransomware: HowDecrypt virus removal tool

Not every old sample of data-encrypting ransomware goes extinct as years go by. The malicious program called CryptorBit fully proves this disappointing trend. It was originally discovered in the wild back in 2014, so it was one of the pioneers on the crypto virus arena, along with such infamous counterparts as CryptoLocker, CTB Locker and CryptoWall. The offending app in question, though, stands out from the crowd as it implements file encryption in an unusual way.
CryptorBit is also referred to as the HowDecrypt ransomware, the latter standing for the name of a TXT edition of ransom instructions that the infection creates on attacked Windows machines. The ultimate goal of this strain is the same as the objective pursued by any other crypto Trojan out there: to defraud computer users of their money. The most important thing that people may store on their PCs is personal data, and the perpetrators are perfectly well aware of this. Ransomware operators therefore use their nasty software to lock one’s sensitive files and hold them for ransom. The program under consideration, however, leverages cryptography quite uniquely. It also engages in digital currency mining activity, exploiting the target PC’s resources for this purpose.
Rather than run a cipher against an entire random file, CryptorBit only skews the first 512 bytes of it and then replaces this portion of data with a different header. The original string gets encrypted and concatenated at the end of the targeted item. This somewhat simplistic technique appears to be a win-win for the extortionists, because it allows their malware to encode big volumes of data in a short time, plus the files do become inaccessible. There is no regular software that’s able to open the objects processed in this fashion. Having made these changes, the malicious application adds files that explain the victim how to restore the information. These include the HowDecrypt.gif and HowDecrypt.txt documents.
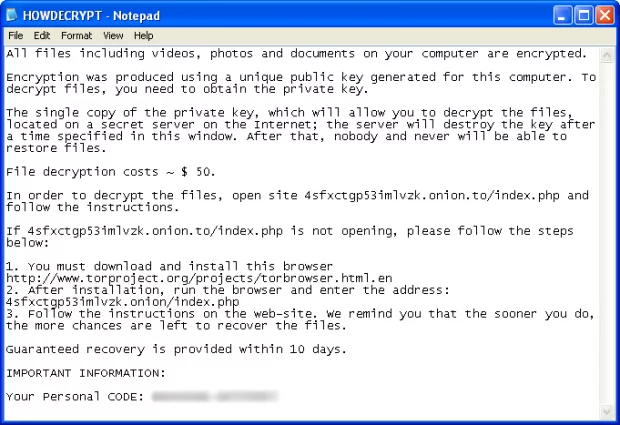
The text within these may vary depending on the particular ransomware version, but most of the time the user will see the following message: “All files including videos, photos and documents on your computer are encrypted. Encryption was produced using a unique public key generated for this computer. To decrypt files, you need to obtain the private key. The single copy of the private key, which will allow you to decrypt the files, is located on a secret server on the Internet; the server will destroy the key after a time specified in this window. After that, nobody and never will be able to restore files.”
The victim is provided with their personal unique code and a Tor gateway to submit the payment. The ransom amount may also vary, but it’s usually in the range of $500. The hackers accept Bitcoins only, indicating the appropriate BTC wallet on the payment page. If the user completes the buyout, they will supposedly receive an email with an archive that contains the CryptorBit Decryptor solution.
The most widespread way the CryptorBit virus enters computers is by means of social engineering, in particular through infectious email attachments. Some experts believe the loader might be executed by attackers via remote access sessions as well. One way or another, if faced with the HowDecrypt threat, users should resort to professional troubleshooting and mitigation techniques.
Table of Contents
CryptorBit (HowDecrypt) ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download CryptorBit (HowDecrypt) ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by CryptorBit (HowDecrypt) ransomware
Workaround 1: Use file recovery software
It’s important to know that the CryptorBit (HowDecrypt) ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether CryptorBit (HowDecrypt) ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓