Cryptonight virus (JS:Cryptonight) removal

There are computer infections like fake system utilities or ransomware that manifest themselves in an outright way. The users hit by the above baddies are shelled by deceptive problem detection reports or simply end up being unable to open their files. The Cryptonight malware is different. It surreptitiously siphons off the host computer’s processing power in order to mine cryptocurrency without the victim’s consent.
Table of Contents
What is the Cryptonight virus?
A little bit of disambiguation from the get-go is definitely appropriate in the context of the Cryptonight threat. It isn’t necessarily an entity denoting malicious activity. In a benign scenario, this concept stands for a popular algorithm used to mine cryptocurrencies, such as Monero or Bitcoin. In plain words, that’s a piece of code that uses the CPU or GPU capacity of a computer in order to verify transactions on the blockchain underlying a specific form of digital cash. This is the way new digital currency items come into existence, and that’s what sets the crypto gaining process in motion. The bad news is that criminals have flipped it all upside down, harnessing Cryptonight to mine XMR or BTC coins without letting the user know.
The malicious routine of the trojanized code in question has got some clear-cut indicators that allow antimalware engines to distinguish it from the legit counterpart. First and foremost, its use of JavaScript is a giveaway – no wonder security solutions usually include the “JS” attribute in the catalogued signature for this perpetrating object. Furthermore, the Cryptonight virus doesn’t employ throttling of any sort, so it tends to crank up the host’s CPU to the maximum. As a result, the processor may fail to cope with the regular tasks, not to mention that it will stay overheated all the time. This is a possible cause for hardware malfunctions as the exploited processing unit will get exhausted sooner or later, so the machine may even crash in the long run. With that said, the culprit has some obfuscation tricks up its sleeve. The malefactors in charge can remotely configure it to be triggered at a certain time, mostly late at night when the victim is less likely to notice the symptoms. It also generates a great deal of network traffic, constantly communicating with mining pools and its Command and Control server.
JS:Cryptonight, which is how this pest is commonly flagged, is doing the rounds in quite a prosaic way. It trespasses on PCs while being a component of software bundles. The scheme is as old as the whole adware industry, which pioneered in leveraging this ruse and still sticks with it. The typical infiltration workflow comes down to furtively attaching the Cryptonight virus to some innocuous and perhaps even useful app. The installation client – at least, its default preset – doesn’t make it clear that any extras are going to be installed along the way, so the target user runs the risk of taking the bait and unknowingly agreeing to the setup of several items. Ultimately, the whole modus operandi of this infection seems to be all about one missing link, that is, user knowledge and approval. It gets into a computer covertly and then doesn’t ask for consent to mine cryptocurrency. Such a blunt piece of code, obviously, isn’t welcome inside a computer, so it’d better be removed as soon as possible if the above shenanigans have been spotted.
Cryptonight adware automatic removal
The extermination of Cryptonight fake can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
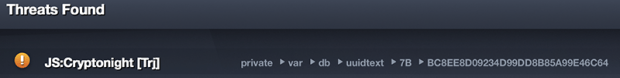
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the malware removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the trojan is gone for good.
Posted in: KnowledgeBase
Leave a Comment (0) ↓