.cryp1 file virus: decrypt and remove CryptXXX 3.0 ransomware

Computer users who happen to fall victim to ransomware don’t have many options to recover their encrypted data. One method is to do what the black hat hackers want, that is, to send the ransom. However, the criminals usually ask for hundreds of dollars, and even those who pay up don’t always get their files back. The other option is to use the best practices of ransomware threat mitigation and file recovery, which is the subject to be described in this article.
CryptXXX 3.0 is a must-avoid piece of software because it grabs one’s personal files, encrypts them and asks for money in exchange for recovery. It is believed to have superseded the previously widespread but now defunct TeslaCrypt ransomware. The threat actors are reportedly using the same readily available malicious infrastructure, including the distribution network, payment processing service and C2 servers. In fact, the compromised Windows users chiefly know this malady by attributes other than its name, because ‘CryptXXX’ isn’t directly manifested in the course of user interaction – that’s what security researchers call it.
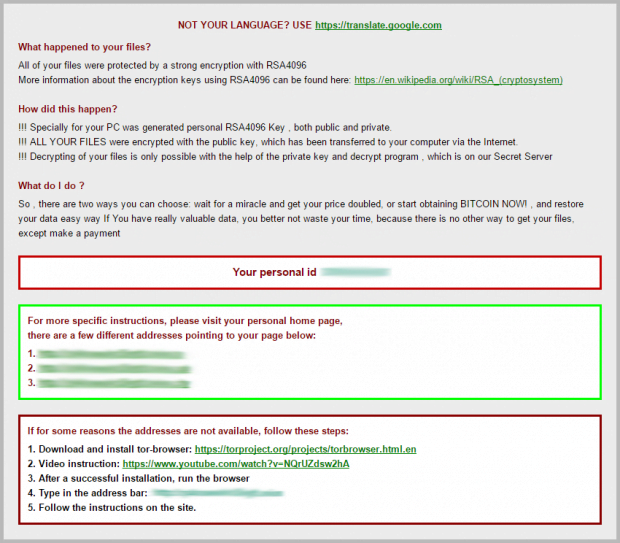
What victims confront is the appending of the .cryp1 extension to skewed files, as well as ransom instructions encapsulated in the following set of documents: !Recovery_[ID].html, !Recovery_[ID].bmp and !Recovery_[ID].txt; or simply the [ID].html and [ID].bmp pair, where the ID parameter is a variable that denotes a unique identifier that the extortionists assign to every attacked machine.
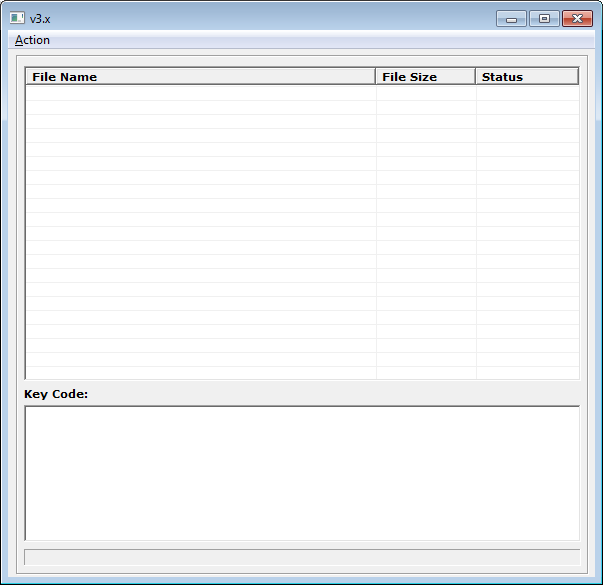
The ransom notes contain several references to RSA4096 or the misspelled variant RZA4096, which is the cryptosystem supposedly used to encrypt files. The analysis of CryptXXX, however, proves a somewhat different approach that the criminals adopt. The ransom Trojan encrypts large byte blocks of any given file with the RC4 stream cipher, and encodes smaller 64 byte blocks with the RSA public-key cryptography. The ransomware doesn’t do a very good job encrypting RC4 blocks, which has allowed researchers to break the crypto in the first versions of this hoax. Now that CryptXXX v3.x has been released, full recovery with specially crafted tools doesn’t appear to be possible.
The .cryp1 extension ransomware targets hundreds of different file formats. It creeps into computers running all editions of Windows through the use of the Angler exploit kit. This tactic makes it virtually impossible for the targeted users to notice the compromise and prevent it. The exploit kit uses weaknesses in out-of-date software and stealthily deposits the dangerous payload on the OS. Incidentally, Angler is also referred to as XXX, so now it’s clear why experts call this ransom Trojan this way.
The malefactors ask for 1.2 Bitcoins for the private key and the decrypt solution. In case the specified time limit for payment is exceeded, the ransom will double and amount to 2.4 Bitcoins, or about 1000 USD. There has been a great deal of feedback about the fact that the decryptor downloaded after the payment doesn’t work and simply returns an error. So users should think twice before sending the ransom. Instead, wait for a likely breakthrough in restoring .cryp1 files or follow the instructions below to get the job done right away.
Table of Contents
.cryp1 files file automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download .cryp1 files ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the file and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by .cryp1 files file
Workaround 1: Use file recovery software
It’s important to know that the .cryp1 files file creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the file under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether .cryp1 files file has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the file itself does not belong inside your computer. Incidentally, it often comes with other file, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this file and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓