ColdLock ransomware: ransom.msil.coldlock.ypae-a virus decryptor and removal

Breaking cybersecurity news is the release of a new ransomware species used in targeted attacks against organizations. It’s called ColdLock, which is a term coined by researchers who unearthed this strain and inspected its modus operandi. The infection has hit a number of networks in the East Asia region so far. Keep reading to find out how it operates, what symptoms it causes, and how to address the issue.
Table of Contents
What is the ColdLock ransomware?
ColdLock is a ransomware threat discovered in early May 2020 in the course of incident response pertaining to a number of companies based in Taiwan. Also identified as ransom.msil.coldlock.ypae-a or ransom.ps1.coldlock.ypae-a, the malicious program contaminated the enterprise networks in a highly covert way, encrypted a plethora of valuable files, and blemished them with the .locked extension. One particularly adverse effect manifested itself during these initial raids: the attackers primarily focused on databases and email servers, arguably the most sensitive and important assets of any business entity. At this point, it’s premature to state whether or not this is a firmly established behavioral pattern of ColdLock ransomware, but if so, it’s definitely bad news for any would-be victim. According to analysts’ preliminary findings, there is a good deal of code overlap between this infection and EDA2, a ransomware originally created for “educational” purposes but later weaponized in real attacks. How exactly the crooks have repurposed the likely prototype remains to be seen.
As mentioned above, ColdLock ransomware is a pivot of targeted attacks that have been isolated to a particular country thus far. The practice of homing in on networks rather than individuals is a long-running hype train in the e-extortion environment. Obviously, there is a new player in cybercriminal circles that’s prioritizing organizations over other types of potential victims. One more unsettling trend over the past few months is to steal data before it is encrypted and then to threaten to release it for public access unless the ransom is paid. At the time of writing, there is no precise answer if this particular Trojan engages in such foul play. Even if it doesn’t, there is plenty of other trickery in its arsenal.
Its distributors use the target’s Active Directory servers as a Launchpad for lateral movement throughout the domain, which entails the contamination of all computers under the same enterprise umbrella. This quirk brings up yet another question: how do the felons access the Active Directory, in the first place? A probable entry point is an RDP hack or an exploit kit that uses a known software vulnerability to inject malicious code behind the scenes. A very offbeat characteristic of the ColdLock virus is that it won’t be executed before 12:10 p.m. This time restriction could be aligned with a particular company in the malefactors’ spotlight. It may as well be a universal rule that’s in effect regardless of the victim. Again, a question with no clear-cut answer for the time being.
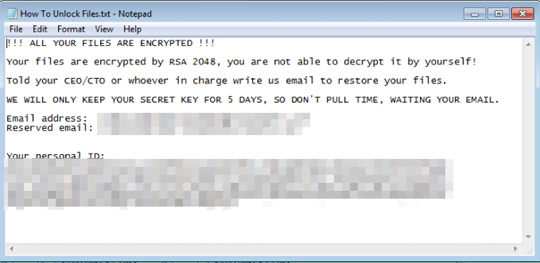
Once the threat maxes out in terms of the number of machines it can infect on the network, it looks for files to encrypt. It comes with a hard-coded blacklist of system-critical files that are skipped during the scan. Then, the malicious encryption process commences in the background. All of the organization’s data that meets predefined criteria is scrambled using AES cryptographic algorithm. A byproduct of this routine is the .locked extension added to the original filenames. The ransom.msil.coldlock.ypae-a virus also drops a recovery note named “How To Unlock Files.txt” and replaces the desktop wallpaper with an image that instructs the victim to read this TXT file. It specifies a five-day deadline for payment otherwise the private decryption key will be allegedly erased. The manual additionally provides the attackers’ email addresses and the victim’s personal ID that should be sent in a message to the extortionists. They will reply with the size of the ransom and the destination Bitcoin address for payment.
No matter how important the hostage data is, though, the ransom method is not recommended. A good starting point for handling the attack is to get rid of the harmful program, if it hasn’t triggered a self-destruct mechanism. Next, try an effective file recovery solution that may be able to retrieve some of the inaccessible data without you having to negotiate with the criminals. Below is a summary of these techniques.
ColdLock ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download ColdLock ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by ColdLock ransomware
Workaround 1: Use file recovery software
It’s important to know that the ColdLock ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether ColdLock ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓