Clop ransomware virus removal and .clop files decryptor
Old strains of ransomware, which nearly disappeared from security analysts’ radar, are reviving. The .Clop file extension specimen is like an echo from the not-so-distant past as it represents the CryptoMix family that hasn’t been updated for months. With this new iteration, the tactic of the malefactors appears to have had an overhaul. Read more to find out what has changed and why the newbie in question is shaping up to be a major issue.
Table of Contents
What is the Clop ransomware?
The stagnation in the ransomware-based extortion underground doesn’t appear to live up to the hopes of security researchers. Not only do massive outbreaks of relatively new strains continue to occur regardless, but some oldies are making themselves felt again. The sample of file-encrypting menace referred to as the Clop ransomware is the latest persona in the CryptoMix lineage, which made its debut back in 2016. It got its name from the .Clop or .CIop extension that the pest appends to the encrypted files. This being a fresh IOC (indicator of compromise), another one is an updated ransom note named ClopReadMe.txt. As before, the cryptographic procedures are immaculately carried out so that the data recovery isn’t viable without the privacy decryption key at one’s disposal. Since this key is in the attackers’ possession, the incursion is still a serious predicament where victims encounter a dilemma: to pay or lose the files.
The above tweaks are certainly conspicuous for those who keep track of the evolution of once prevalent ransom Trojans. However, there are much more disconcerting alterations on the inside as well as spreading-wise. Whereas CryptoMix originally zeroed in on separate PCs, the Clop ransomware spinoff has changed the tactic by focusing on computer networks. This approach introduces substantial benefits for the crooks. First off, hitting a large enterprise environment means a stronger position of the attackers in their negotiations with the compromised organization, hence higher ransoms that can be extorted. Secondly, the contamination proper doesn’t rely on large-scale malspam campaigns reminiscent of shots in the dark – instead, it is a targeted process. The most likely breach vectors are RDP hacks or phishing that entails network administrative credentials being wheedled out.
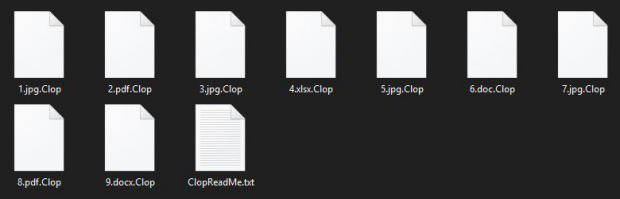
A number of behavioral quirks of the Clop ransomware make it a unique piece, too. Its binary boasts a valid digital signature, therefore some antivirus tools may fail to identify it as a threat at the early stage of the attack. Once on board, the culprit tries to terminate several Windows processes, thus ensuring that the files used by them aren’t in use and can be encoded. Yet another offbeat feature of the infection is that it drops a batch file that, when fired up, performs a series of commands to break data recovery through shadow copies. Next comes the encryption workflow, something that’s done flawlessly and doesn’t yield to cracking via brute-force or similar techniques. An outer byproduct of the data skewing is the concatenation of the .Clop or .CIop (with an uppercase “i”) to every filename. Therefore, having encrypted a sample file named Landscape.jpg, the baddie transforms it into Landscape.jpg.Clop.
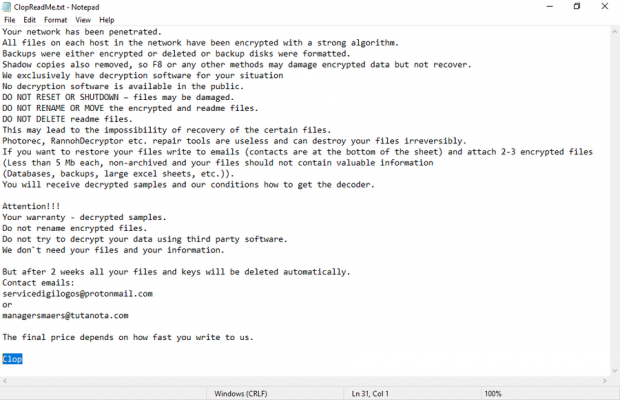
The ClopReadMe.txt ransom note is verbose and has an introductory phrase “Your networks has [sic] been penetrated”. It emphasizes that resetting or shutting down the machine may damage the data. The malefactors also offer free decryption of 4-6 files containing no valuable information. The contact emails at the bottom of the note are the only way to reach out to the attackers. While these vary from incident to incident, the frequently reported ones include unlock@eqaltech.su, unlock@royalmail.su, kensgilbomet@protonmail.com, servicedigilogos@protonmail.com, and managersmaers@tutanota.com. The victim is instructed to indicate their company name and website in the email, which is one more clue that the focus of the perpetrators has shifted from personal computers to business networks. All in all, it appears that the comeback of CryptoMix in its .Clop file incarnation has worked out, and unfortunately there is no reliable method to defeat its crypto so far. A few tips and tricks are worth trying, though. Learn what they are and get rid of the Clop ransomware right away.
Clop ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Clop ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Clop ransomware
Workaround 1: Use file recovery software
It’s important to know that the Clop ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Clop ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓