Chromesearch.today removal from Chrome, Mozilla Firefox and IE
A new browser-borne infection, chromesearch.today, has been taking the cyber world by storm over the past few weeks. On the face of it, this pest seems like a garden variety search provider. That’s a delusive impression, though. It is actually bolstered by a massive wave of malware distribution. Keep reading to learn all the whats, the whys and the hows regarding this issue.
Table of Contents
What is the chromesearch.today virus?
To grasp the gist of the digital baddie in question, it makes sense to first dissect the nature of a regular browser extension in a nutshell. Also referred to as add-ons or browser helper objects, these pieces of software are plugged into one’s web navigation client in order to enhance certain areas of Internet surfing. A commonplace ad blocker or video downloader exemplifies this concept quite accurately. Every legit add-on should, ideally, ask for user permission when making changes to online presets and won’t apply them unless allowed. Now, one of the reasons the chromesearch.today entity is different is because it calls forth changes without proper authorization. That’s what makes it a PUP (potentially unwanted program). What are these modifications that end up becoming such a nuisance to end users? Let’s look into this in detail.
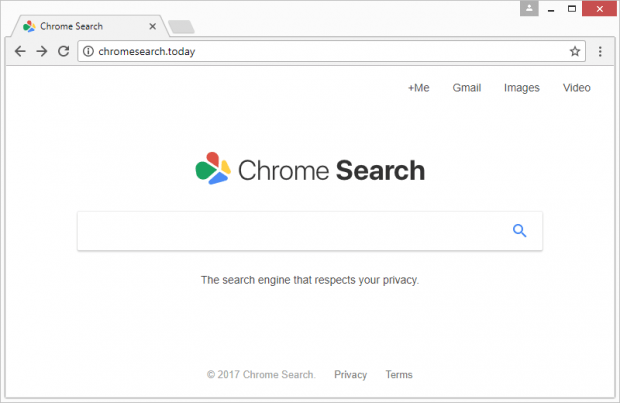
The perpetrating add-on behind chromesearch.today forcibly alters the following browsing settings: homepage, default search engine, and new tab page. This means that whenever a victim opens Chrome, Firefox, IE, or possibly other popular browser they are using, the chromesearch.today or chromesearch.today/search?q=%s URL will be resolved instead of the preferred ones for each of the above values. To top it off, the infection tends to meddle with shortcuts for random applications – it replaces the correct address string in the Target field with the wrong one so that the user visits the rogue landing page whenever they open the utility. The site itself is titled “Chrome Search” and imitates the look and feel of Google. There seem to be no defiant red flags in it.
Why then do the ne’er-do-wells in charge of this campaign want people to get stuck in this loop of hijacks and redirects? Traffic monetization is the answer. The more users visit chromesearch.today the more ad views and leads the threat actors get. These things are paid for these days. Interestingly, the malicious website features a logo that says, “The search engine that respects your privacy.” That’s a really ironical statement, given that the hijacker harvests users’ online data behind the scenes. It collects information on a prey’s Internet surfing preferences, including sites visited, search queries made, bookmarked pages and the like.
When it comes to the troubleshooting for some plagued users, one of the biggest problems about the chromesearch.today virus is that it adds a new Chrome policy. This trick ensures persistence of the adverse effect, preventing the user from undoing the changes manually. Therefore, a full-fledged fix takes more than the regular disabling of a browser extension that’s acting up. The walkthrough below covers all the remediation options that work in this predicament.
Chromesearch.today hijacker automatic removal
The extermination of Chromesearch.today PUP can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Chromesearch.today remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the hijacker removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the hijacker is gone for good.
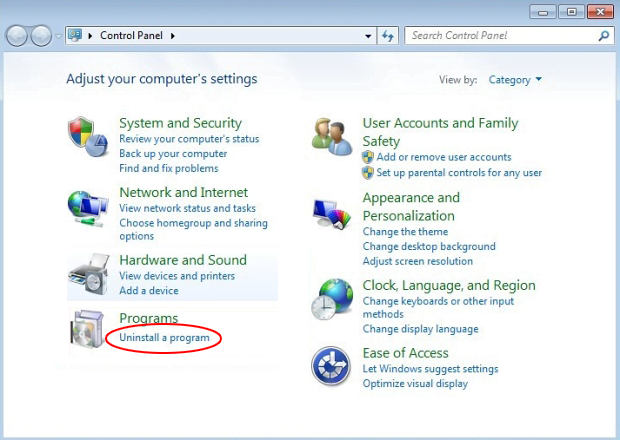
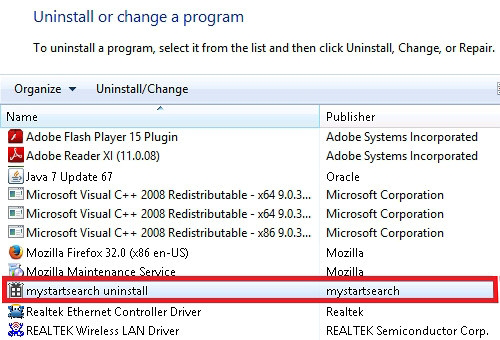
Remove Chromesearch.today hijacker using Control Panel
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Chromesearch.today hijacker removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
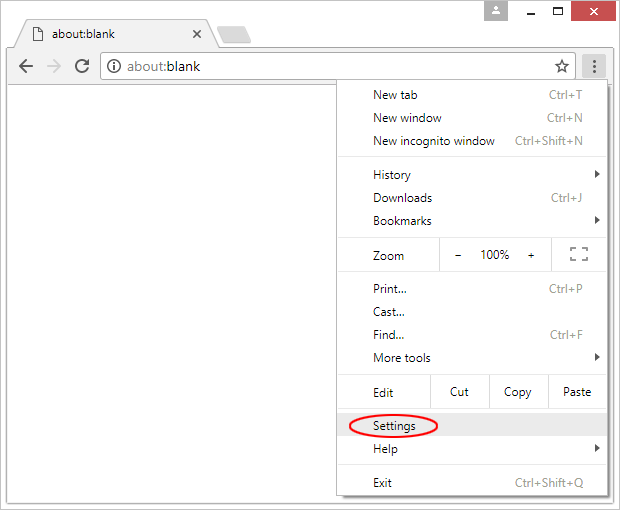
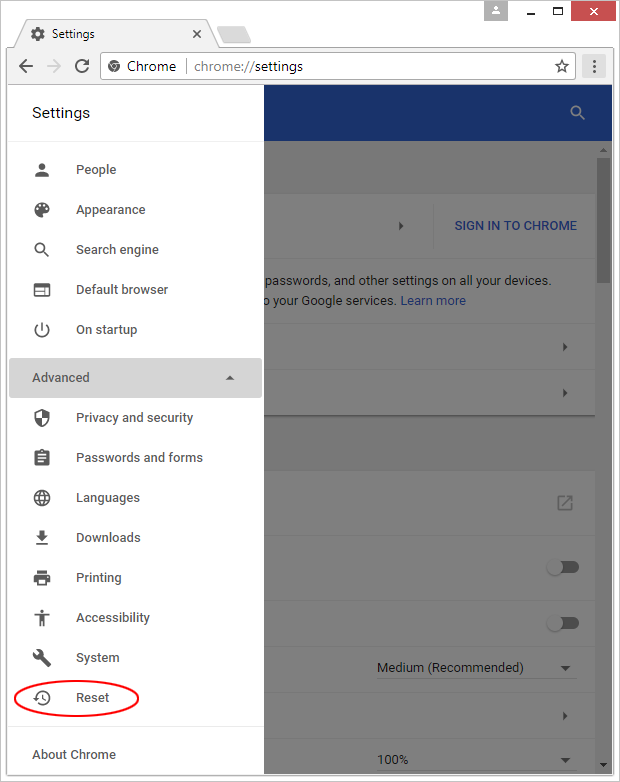
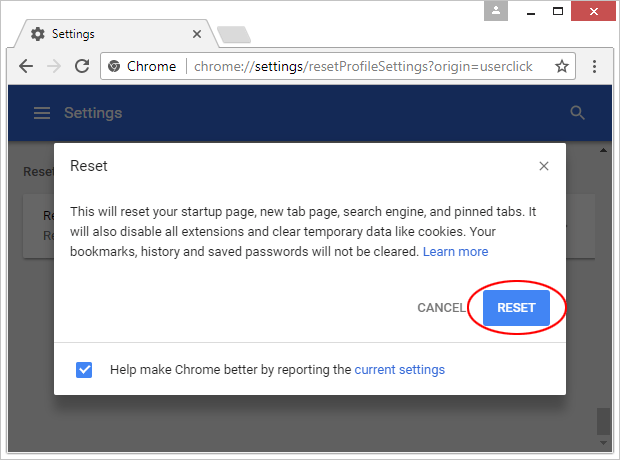
Reset Google Chrome
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

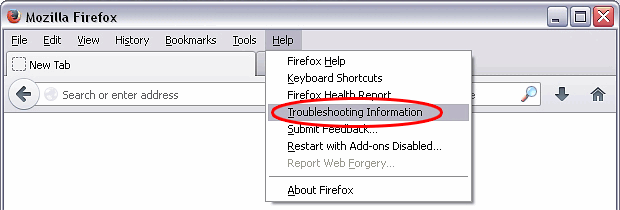
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

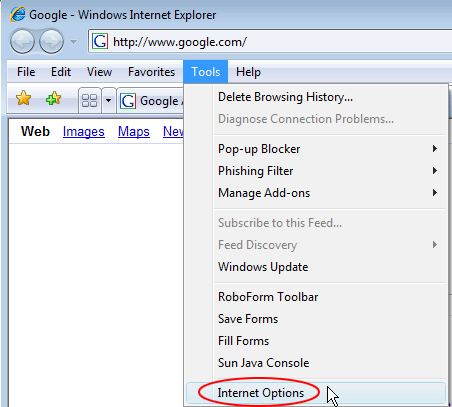
Reset Internet Explorer
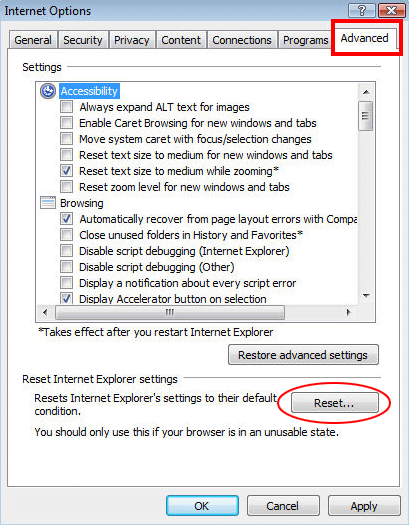
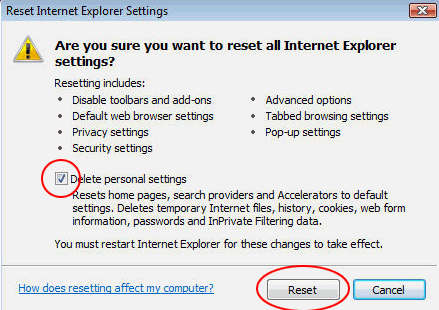
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether Chromesearch.today hijacker has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this PUP are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓