Cerber2 ransomware virus decryptor and removal
There is a bevy of details and ties that can be deduced from just the name of the latest crypto infection dubbed “Cerber2”. The symptoms of an assault by this new ransomware threat include a muddle of encrypted, hence inaccessible .cerber2 files spawned across the infected computer, as well as scary warning messages that ask for Bitcoins. This guide dissects the plague, lists its connections with a forerunner, and provides mitigation advice.
The resiliency of ransomware infrastructure varies from sample to sample, where no such thing as “average” is in place. Whereas some Trojans don’t use C2 servers to operate the exchange of private crypto keys, others do. Also, there are strains that feature interaction with victims via email only, while others have it all automated through a specially crafted web interface. The one in question, referred to as Cerber2, goes the most technically sophisticated route. It borrowed most of its high-profile characteristics from the predecessor called Cerber proper, including the names of ransom notes and the encryption standard. However, these malign properties have been enhanced, plus there are new ones that are unique for this breed.
This offending program can end up on a Windows PC in several ways. The common delivery technique involves phishing, where a user gets an incoming booby-trapped email with a harmful attachment disguised as an invoice, tax papers, UPS tracking report or similar. In this scenario, prevention is a function of not opening dubious-looking ZIP or Docm (Microsoft Office document with macros) email attachments. The other vector of propagation is based on the phenomenon of exploit kits. Under these circumstances, the only thing that can really aid and thwart infection is patched software on the machine, otherwise the ransom Trojan will be deployed unnoticeably when a hacked web page is visited.
Quite predictably for this family, Cerber2 finds and encrypts most of the files stored on local drives, network drives and removable devices. The exceptions include auxiliary elements that keep the operating system run smooth. Personal files undergo a bad scrambling with an algo called the Advanced Encryption Standard, or AES. As opposed to the use of 16-byte keys by the previous edition of Cerber, the new incarnation generates 32-byte ones. This, naturally, makes data recovery further aggravated. The format of encrypted files changes as well – the infection replaces original filenames with 10 hexadecimal characters plus the .cerber2 extension. The forerunner didn’t do this.
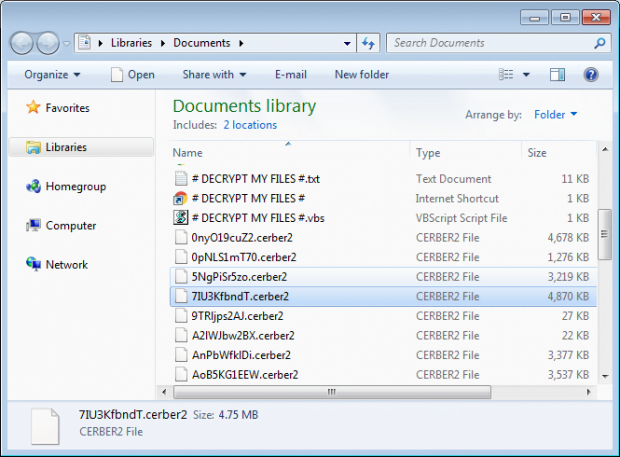
As soon as the ransomware is through with the crypto part of the compromise, it starts communicating with the victim regarding the ways out. To this end, it creates a number of new entries within every directory that holds encrypted files, namely # DECRYPT MY FILES #.html, # DECRYPT MY FILES #.txt, and # DECRYPT MY FILES #.vbs. Incidentally, the latter is liable for playing an audio alert in the background that says, “Your documents, photos, databases and other important files have been encrypted.” To top it all off, Cerber2 changes the desktop wallpaper and displays its demands in such a blatant fashion, too.
The workflow of recovery imposed by the virus involves a Tor page to which the infected user is directed. Titled “Cerber Decryptor”, this page clearly expresses the cybercrooks’ demands: the person needs to submit about 1.5 BTC to a certain Bitcoin wallet during 5 days, or else the ransom will double. The Cerber version 2 ransomware, regretfully, is too strong encryption-wise to crack, which doesn’t spare much room for maneuver. Some of the applicable tactics of data restoration are covered below, although there can be no certainty that they will do the trick. There is no harm in trying, though.
Table of Contents
Cerber2 ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Cerber2 ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Cerber2 ransomware
Workaround 1: Use file recovery software
It’s important to know that the Cerber2 ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Cerber2 ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓