.BIP ransomware decryptor and removal tool
Some ransomware lineages don’t seem to have been impacted by the general plummeting of the crypto extortion epidemic. One of these families known as Dharma, or CrySiS, continues to be a serious concern as it spews out new versions regularly. Its most recent mod appends the .bip extension to encrypted files. Keep reading this article to learn more about this iteration and get effective removal advice.
Table of Contents
What is the .bip files virus?
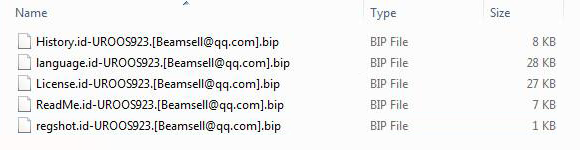
The above-mentioned Dharma ransomware is definitely among the top and most prolific strains around. It has been in massive circulation for more than a year and remains afloat despite the fact that some extortionist groups have abandoned the “business” and turned to more lucrative moneymaking tactics, such as cryptojacking. The malicious code in question is apparently undergoing continuous evolutionary processes, spawning new builds once in a while. The latest one concatenates the .bip extension to the files it takes hostage. This tail is prepended by a victim ID plus the malicious agents’ contact email address, which varies in different campaigns and also depends on the cybercriminal crew distributing the sample on a Ransomware-as-a-Service (RaaS) basis.
The resulting mutation of a sample filename Camomile.jpg is therefore going to be as follows: Camomile.jpg.id-CFBCA710.[buydecrypt@qq.com].bip. The 8 hexadecimal characters reflect the victim’s unique identifier. Again, the email string can be different than the one indicated in the example. Some other commonly reported ones include restoresales@airmail.cc, beamsell@qq.com, paymentbtc@firemail.cc, and return24data@cock.li. Whereas the external skewing of one’s files due to the attack is quite dramatic, the biggest impact is on a deeper level. The .bip Dharma ransomware applies a strong cryptographic algorithm, typically a mix of symmetric AES and asymmetric RSA ciphers, in order to badly scramble the inner structure of data. Such a tampering results in the victim’s personal files getting locked down, where the recovery is a no-go unless the plagued user gets the private decryption key.
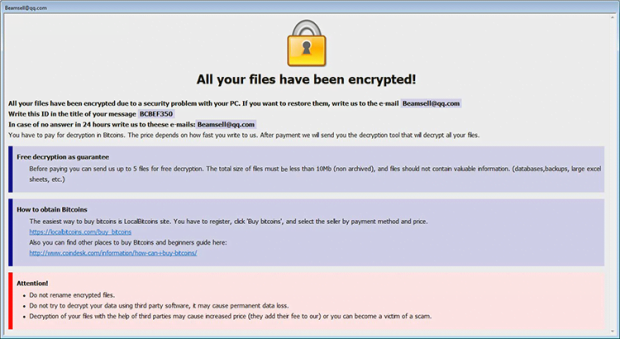
The problem is, the secret key is kept by the attackers and, according to their claims, will be provided to the victim once a ransom is submitted in Bitcoin. This is what ransom Trojans are all about, so those infected are confronted with a tough dilemma – possibly lose files or pay up. Even if the latter option is picked, though, there can be no certainty that the miscreants will follow through on their promises.
Zooming out, the attackers additionally provide a recovery walkthrough. In the .bip files virus scenario, these so-called ransom notes come in two different formats. One is a file named Info.hta (see image above). It is configured to pop up automatically after user logon and includes the standard Dharma ransomware warning “All your files have been encrypted!” as well as instructions on how to reach out to the crooks and get the decryptor. Another version of the how-to’s is named FILES ENCRYPTED.txt. It isn’t as verbose as the HTA counterpart and only tells the user to shoot a message to the indicated email address paymentbtc@firemail.cc.
This infection mostly arrives at computers through improperly protected remote desktop services. The threat actors brute-force RDP credentials and install the culprit manually. That’s some food for thought regarding users’ security hygiene. Ransomware prevention isn’t restricted to refraining from opening spam email attachments these days, so be sure to also secure your RDP activity.
To recap, the .bip variant of Dharma ransomware is just as harmful as the previous .bip file edition. It prevents victims from accessing their valuable data and extorts up to 0.5 BTC for recovery. The steps below may help reinstate hostage data without following the ransom demands. Give it a shot and see what’s recoverable via data forensics.
.BIP extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download .BIP ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the extension and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by .BIP extension
Workaround 1: Use file recovery software
It’s important to know that the .BIP extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether .BIP extension has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the extension itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓