Decrypt and remove Bart ransomware (.bart.zip extension virus)
A new breed of Internet scum named the Bart ransomware entered a rapid circulation phase last weekend, with hundreds of Windows computers reportedly affected at the time of writing. Despite the apparent fact that the ransom instructions and the payment page design are nearly identical to those used by another plague called Locky, the principle of data jumbling is absolutely different. The Bart Trojan makes one’s files morph into ciphered, password-protected archives with .bart.zip extension.
When this sample first drew researchers’ attention, it became clear that the imminent extortion hoax was going to be massive. The bulk spam campaign, which aims at depositing Bart onto PCs, is too large-scale for a ransomware underdog. Numerous users have been receiving tricky messages over email, most of which are associated with photos. It’s hard to think of a more enticing subject than pictures, so no wonder lots of people end up opening those attachments. What actually happens when they do is a malicious JavaScript code runs and installs the infection without giving much chance for the user to realize how destructive this may be. An interesting fact is that the Trojan determines the system language of a breached machine and uploads the appropriate set of ransom notes.
The Bart ransomware targets more than 100 data formats, including popular ones like .avi, .bmp, .cmd, .crt, .csv, .doc(x), .flv, .gif, .jar, .java, .jpeg, .jpg, .mkv, .mov, .mp3, .mp4, .mpeg, .pdf, .php, .png, .ppt(x), .rar, .rtf, and .xls(x). After the unauthorized processing of these objects has been completed, they will have the .bart.zip string at the end. For example, a sample item ‘episode1.mov’ becomes ‘episode1.mov.bart.zip’. In order to open the ZIPs and access their contents, the victim needs a password that only the criminals have. This is an entirely new approach to locking information – instead, ransom Trojans tend to straightforwardly apply symmetric or asymmetric ciphers, or both.
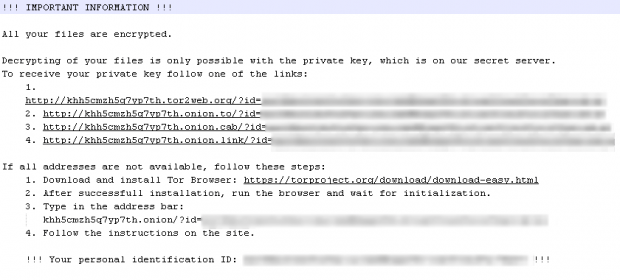
To shed light on what’s going on, Bart creates a myriad of files named recover.txt all over the infected system. These Notepad documents appear inside folders and on the Desktop. By the way, the malicious program also sets the recover.bmp image as the Desktop background. Both of these editions of recovery instructions read “!!! Important Information !!! All your files are encrypted”, and contain four Tor (The Onion Router) links to follow, which provide the actual decryption workaround. In the event the user cannot access those links, they are told to install the Tor browser. Another important piece of data included in recover.txt and recover.bmp files is the victim’s unique ID that serves as their personal identifier for the payment of ransom.
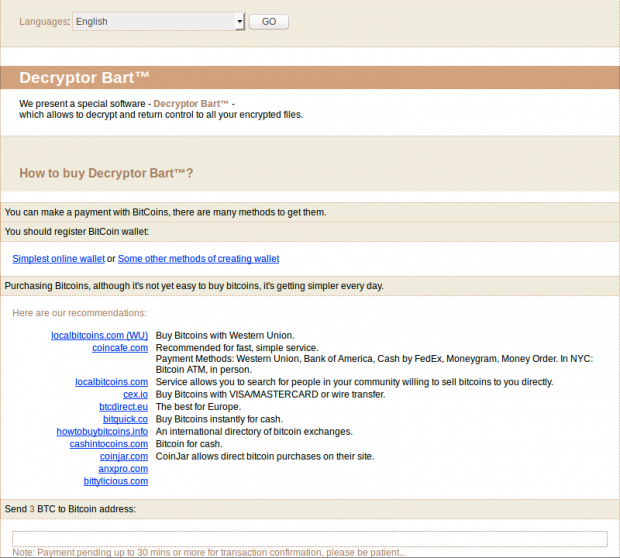
The linked-to page titled “Decryptor Bart” further instructs the user to send 3 Bitcoins, which is a little under 2000 USD, in order to obtain the password for accessing the locked data. There is no payment deadline clearly indicated anywhere on the ransomware screens, but the size may increase if the victim lingers with the buyout.
Similarly to the above-mentioned Locky infection, the distribution of the Bart ransomware involves a component known as RockLoader. The use of this go-between program makes the attack process smooth and prevents antimalware engines from detecting the virus. All in all, this is a sophisticated contagion that poses quite a challenge to security vendors and other ransomware fighters. While brute-forcing of the passwords that unlock Bart-encrypted ZIP archives has been to no avail thus far, the infected users should start with alternative file recovery methods.
Table of Contents
Bart extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Bart ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the extension and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Bart extension
Workaround 1: Use file recovery software
It’s important to know that the Bart extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Bart extension has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the extension itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓