BadBlock ransomware: remove virus and restore files

The appending of specific extensions to encrypted files is the feature du jour in the average ransomware’s operational arsenal. One of the latest strains, however, appears to neglect the malware underground vogue as it doesn’t concatenate anything to filenames of blatantly locked data elements. This ugly duckling is called BadBlock, and it’s just as dangerous as its better-known counterparts despite the lack of filename skewing effect.
The sample under analysis is a growing menace that holds one’s files for ransom, demanding that the infected users pay 2 Bitcoins to redeem their important data. That’s approximately 900 USD, so the stakes are high. BadBlock relies on a ramified circulation methodology, with phishing and exploit kits being the primary instruments on the extortionists’ hands. The former technique is in fact unsophisticated social engineering, where all it takes to fulfill a breach is simply convince a targeted person to open an email attachment with the malicious loader on board. Another tactic is based on the use of offending software that injects the trojanized payload into an operating system via zero-day vulnerabilities in programs that weren’t patched for quite a while.
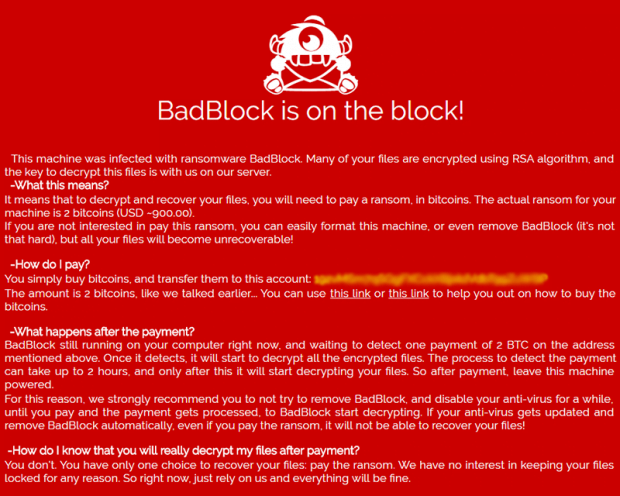
If any of the above stratagems end up being successful, the ransomware creates several executables, including badblock.exe and badransom.exe, and drops a detailed avenue on file recovery named “Help Decrypt.html”. This document makes the victim aware of the attack and the fix through the following text: “This machine was infected with ransomware BadBlock. Many of your files are encrypted using RSA algorithm, and the key to decrypt these files is with us on our server. What this means? It means that to decrypt and recover your files, you will need to pay a ransom, in bitcoins. The actual ransom for your machine is 2 bitcoins (USD ~900). If you are not interested in paying this ransom, you can easily format this machine, or even remove BadBlock (it’s not that hard), but all your files will become unrecoverable.”
The scoundrels also provide a Bitcoin address that the user should use to submit the ransom. Also, they recommend that the victim disable their antivirus software for a while so that it won’t detect and automatically eradicate the ransomware, otherwise decryption allegedly won’t be feasible even in case the payment is sent in.
In spite of the fact that BadBlock looks rather professionally crafted on the outside, it’s got flaws regarding the implementation of the above-mentioned cryptosystem. Furthermore, it may fail to disable the Volume Shadow Copy Service, leaving a viable recovery loophole behind. Therefore, some of the universal ransomware troubleshooting methods are worth a shot in case this infection is inside.
Table of Contents
BadBlock (Help Decrypt.html) ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download BadBlock (Help Decrypt.html) ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by BadBlock (Help Decrypt.html) ransomware
Workaround 1: Use file recovery software
It’s important to know that the BadBlock (Help Decrypt.html) ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether BadBlock (Help Decrypt.html) ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓