Remove akamaihd.net virus in Chrome, Firefox and Internet Explorer

Anyone using popular social networks like Facebook or Twitter have encountered akamaihd.net as a transitional server name when viewing or uploading data. In fact, this URL denotes a powerful cloud network hosting content for a variety of services. Meanwhile, a lot of users are having browser problems symptomized by the above domain being visited at random. Find out how and why this generally utile provider is being misused by cybercriminals out there.
First and foremost, akamaihd.net does not stand for a harmful or compromised web page whatsoever. It is essentially an authoritative CDN (content delivery network) whose capacities and features are in demand with a great many online services, including social networks and various ecommerce portals. The main benefit for these companies is they can outsource a significant part of data storage to the third-party entity so that their own infrastructure is relieved from the burden. This way, all parties are satisfied, including the end users who are less likely to suffer from server lags when their requests are being processed. Obviously, malware distributors don’t mind using akamaihd.net to their advantage either, especially considering the very low probability of the unsafe landing pages going blacklisted.
Some of the recent reports regarding this CDN being exploited involve the instances where users’ web browsers start to act up by generating annoying popup windows or randomly opening new tabs. The URLs being resolved in these cases can be as follows: searchinterneat-a.akamaihd.net, rvzr-a.akamaihd.net, rvzr2-a.akamaihd.net, or similar. Whereas the server name proper is static across all these occasions, the prefix is variable as you can see. Normally, these are landing pages that display misleading alerts. The objective of such a technique is to dupe the infected person into downloading and installing a potentially unwanted program or a junk one that’s part of an affiliate marketing scheme.
Sometimes there are no download recommendations on the sites redirected to via akamaihd.net. The victims may end up on search engines, both reputable such as Yahoo.com and pretty much worthless ones like SearchPile or TopArama. None of these hits are authorized by the user – it’s actually a browser hijacker to blame for the mishap. Prior to the occurrence of this issue, one’s computer gets infected by a deleterious code in the course of a free software setup that incorporates a bundle complementing the core product. It’s hard to spot the threat at that point, so the malware usually trespasses on computers unobstructed. It then integrates a malicious plugin in the Internet browsers so that duplicitous pages ending with “akamaihd.net” are recurrently visited. The users find it hard to locate the mischievous browser component and uninstall it, so they should run an antimalware tool, stick to manual remediation steps, or combine the two techniques for a successful outcome.
Table of Contents
Akamaihd.net adware automatic removal
The extermination of Akamaihd.net hijacker can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the adware removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the adware is gone for good.
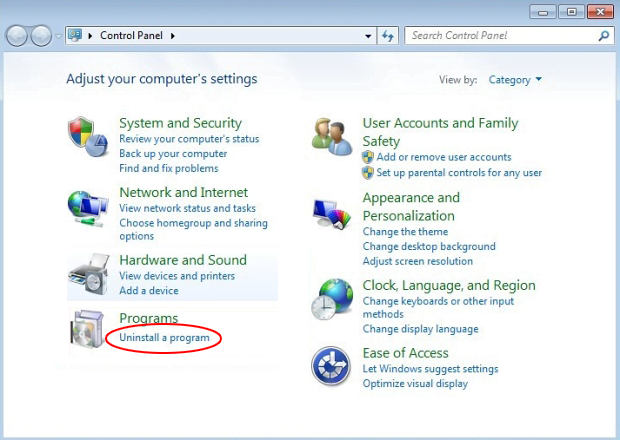
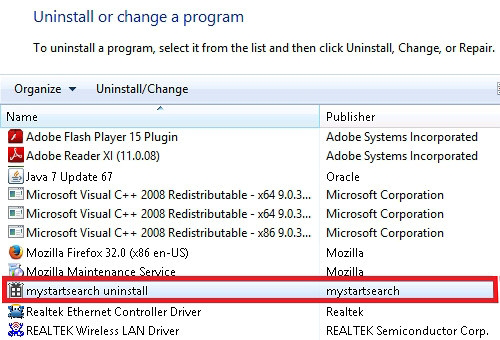
Remove Akamaihd.net adware using Control Panel
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Akamaihd.net adware removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
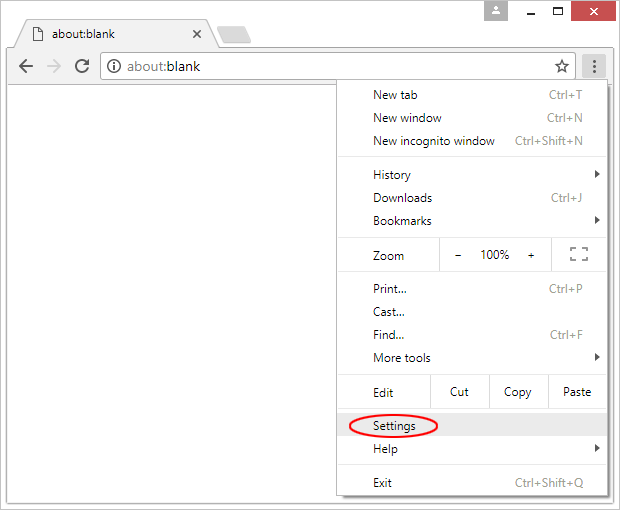
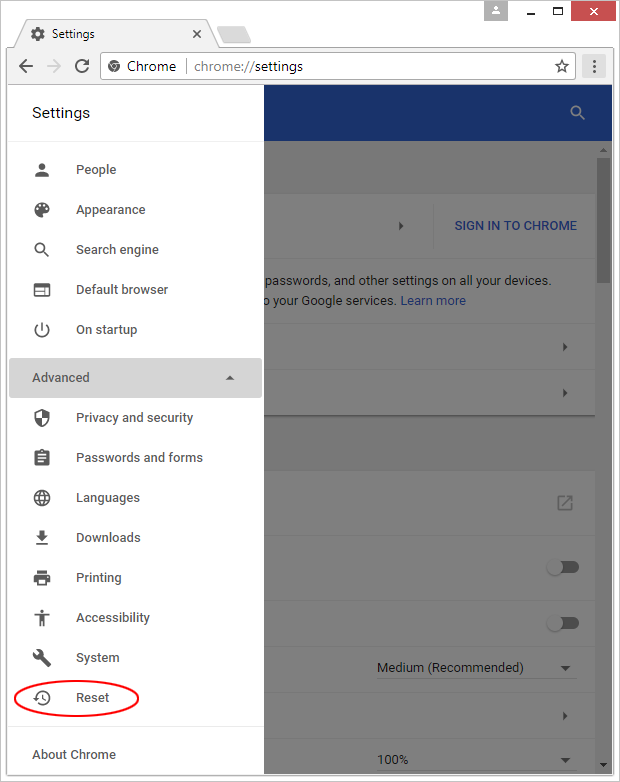
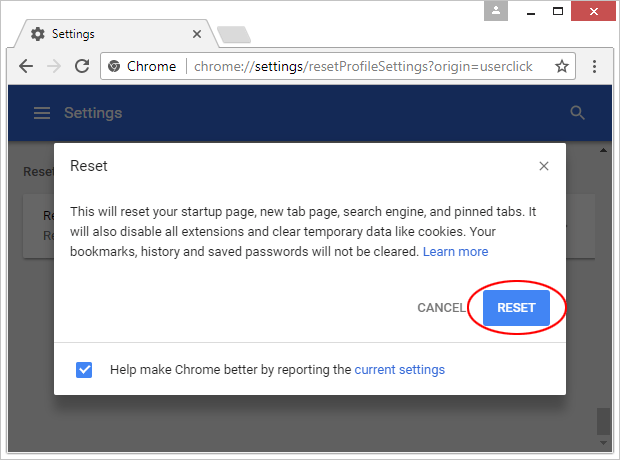
Reset Google Chrome
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

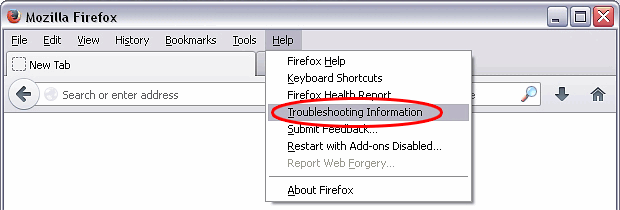
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

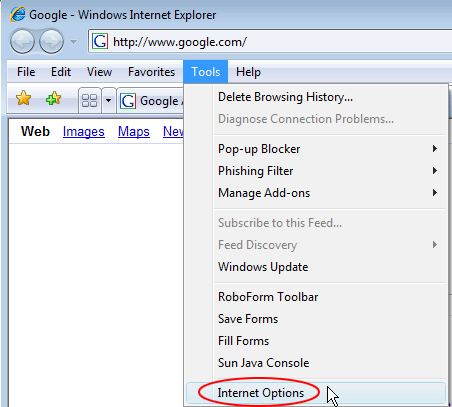
Reset Internet Explorer
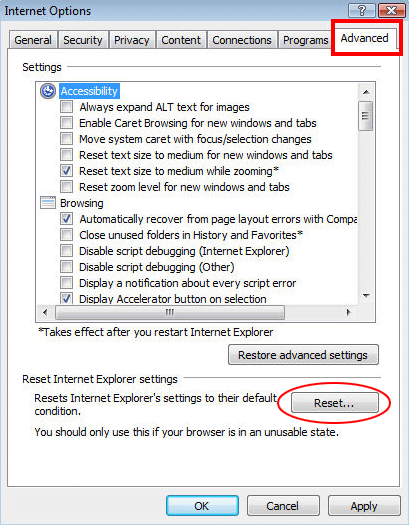
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

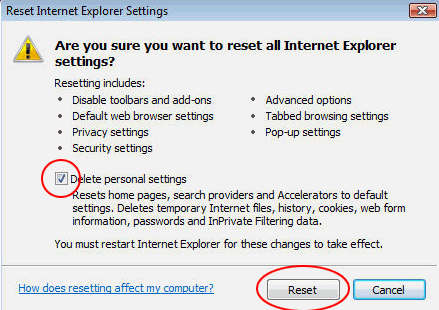
- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether Akamaihd.net adware has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this hijacker are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓