Ads by Provider removal in Chrome, Firefox and Internet Explorer

To procure assistance in the domain of online advertising, the easiest path merchants can go is sign up with a platform that links their sites with the potential end users. Ideally, this scheme works flawlessly for everyone involved, but with the digital facility that powers ‘Ads by Provider’, the outcome is a complete bummer for the consumers. The advertisements are irritating because people do not opt into viewing them.
Some toolbars, extensions or plugins purportedly tailored to sustain e-marketing activity can cause a great deal of inconveniences to those who happen to install them. Things get yet worse in the event this setup takes place through a course of action that excludes the computer user’s agreement from the set of prerequisites for the completion of said process. This, unfortunately, isn’t an uncommon encounter nowadays, given the ubiquity of adware threats which have come to occupy one of the dominating positions in the global cybercrime structure. The issue of Ads by Provider literally jamming up web pages is a classic example of a latent adware attack aftermath. Infected users keep on bumping into numberless floating windows, banners, coupons, chunks of inline text as well as interstitial ads wherever they go on the Internet.
Just like any other malware, the Ads by Provider snag on a PC stems from a prior injection of the detrimental code. Since no sane person is their computer’s foe, the assault is performed inconspicuously. This particular specimen diffuses mostly by means of bundling, which is a process where third-party applications are integrated into a client originally designed to install another piece of software. In some cases, the additions are not listed in the open therefore users are deliberately duped into installing the compound package in one shot. Aside from this technique, the adware threat known as Techsnab was found to also push the pest in question via a drive-by routine.
The Ads by Provider virus is indiscriminate regarding the sites that it displays its content on. As long as the malicious executable is running in the system, the advertisements will be presented on search engines, social networks and the rest of regular web pages that the victim visits. Many of these expand from words, which are turned bluish, capitalized and clickable. Some Ads by Provider pretend to be simplistic quizzes, where the user is suggested to click a link, answer several questions and ‘access exclusive offers’. In reality, however, this trick may be used to inject more malware. It goes without saying that such a messy app doesn’t belong on a healthy computer, so get down to retaining the security status quo.
Table of Contents
Provider ads automatic removal
The extermination of Provider malware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the ads removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the ads is gone for good.
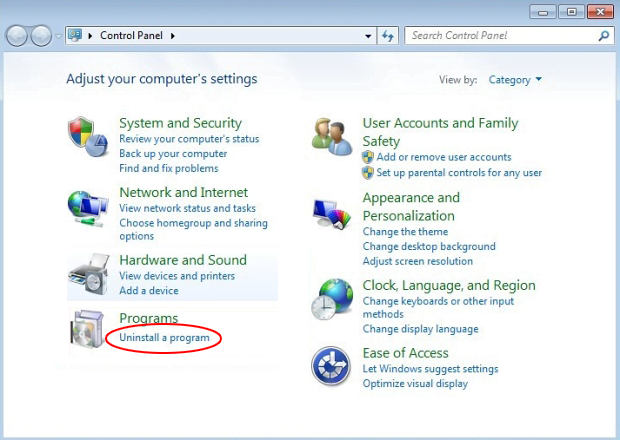
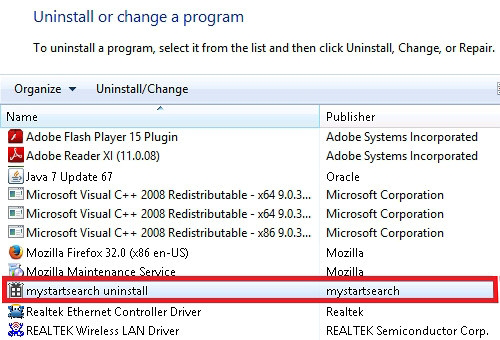
Remove Provider ads using Control Panel
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Provider ads removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
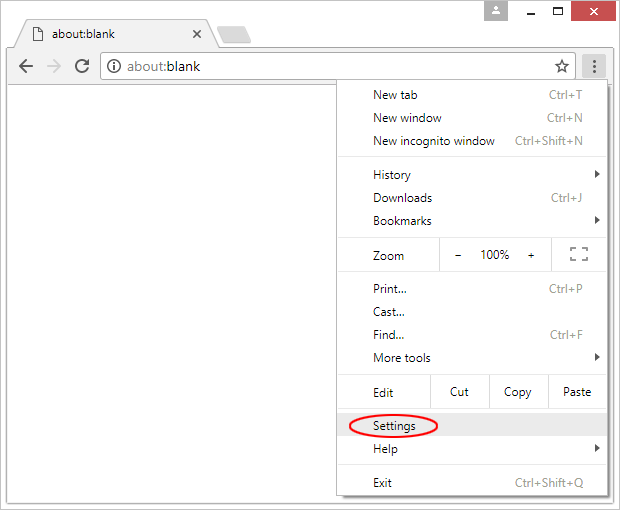
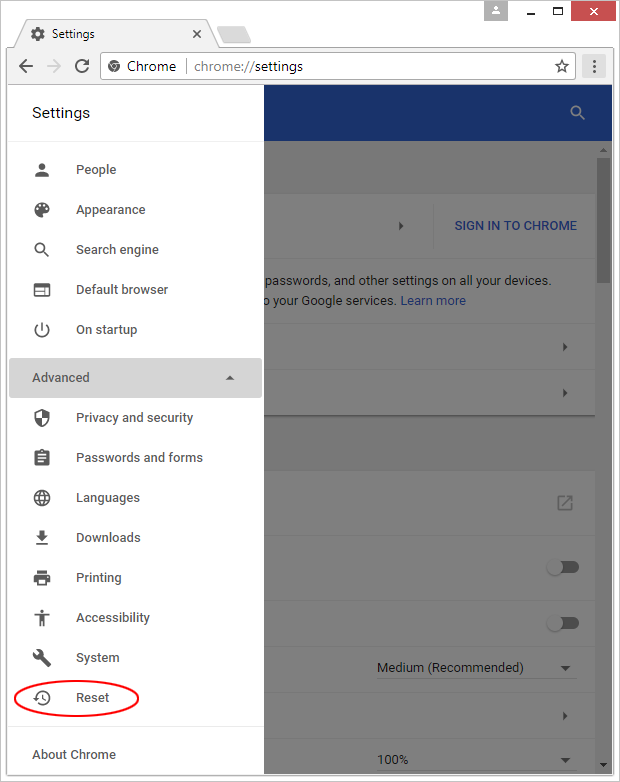
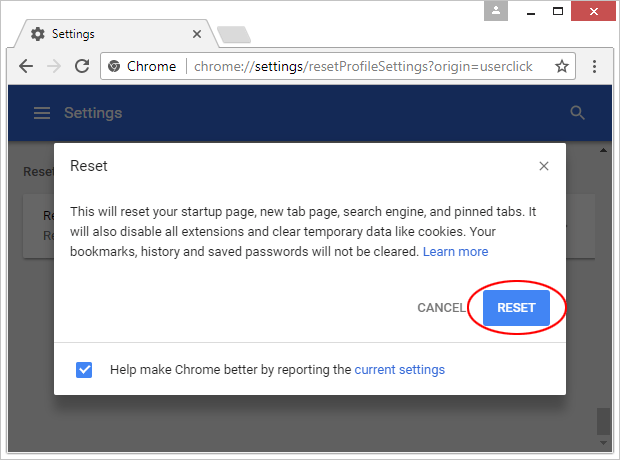
Reset Google Chrome
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

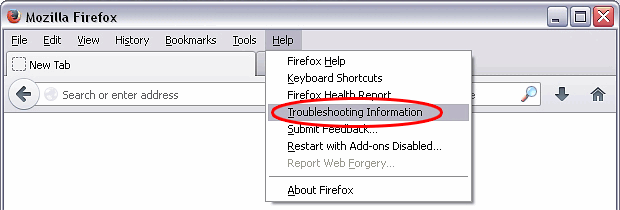
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

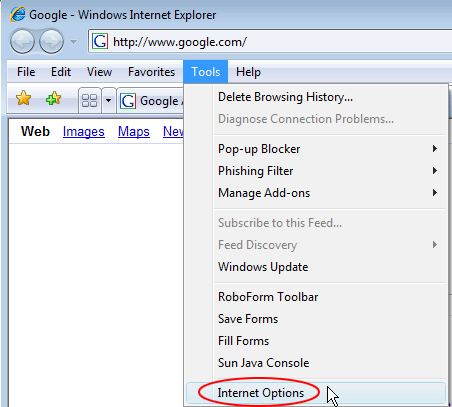
Reset Internet Explorer
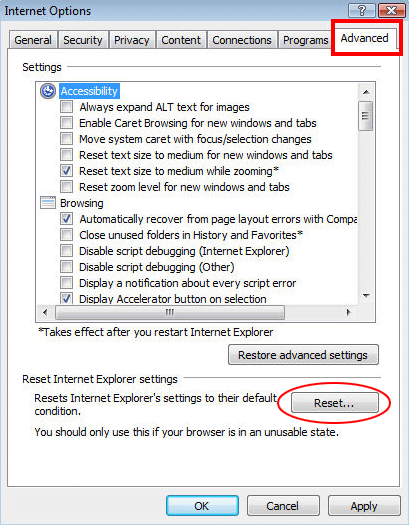
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

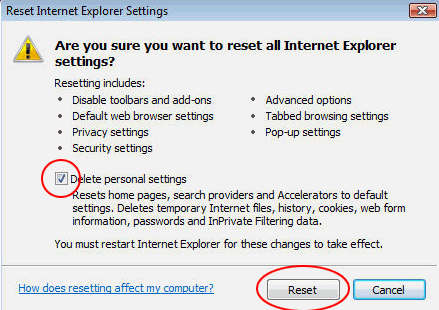
- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether Provider ads has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this malware are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓