Virus HELP_HELP_HELP: Cerber Ransomware 2017 edition decryptor
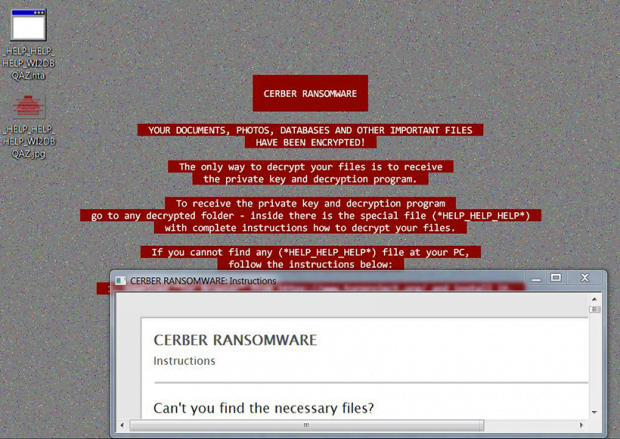
As the Cerber ransomware is approaching a one-year milestone of its abominable extortion crusade, its authors have rolled out another update to give their brainchild a slightly different look and feel. The fresh 2017 iteration currently on the loose sticks with a red color scheme for highlighting the text of the desktop warning. The most significant change, though, is that Cerber has started to drop ransom notes called _HELP_HELP_HELP_[random].hta/jpg.
Table of Contents
What is the HELP_HELP_HELP ransomware?
Again, this is the name of decryption how-to’s created by the latest variant of the Cerber crypto virus. Since HTA and JPG copies of it appear on the desktop of an infected computer and inside most folders, victims often associate their cyber offender with an entity named _HELP_HELP_HELP. Just like previous versions of Cerber, this one is not decryptable, so users are confronted with a dilemma of paying the ransom or losing important data. As opposed to its precursor, the new edition does not disclose its version number anywhere in the ransom notes. Although the sophistication of this sample goes off-scale, it arrives at computers in an old-fashion way. The distribution is all about spam. When a rogue receipt or ISP complaint hits a user’s inbox, it evokes the recipient’s natural curiosity and encourages them to open the attached ZIP archive and extract a Microsoft Word document from it.
The above-mentioned tricky file returns an error message when opened. The dialog prompts the unsuspecting user to turn Word macros on, which is definitely a bad idea. As soon as macros are enabled, an ad-hoc script starts running that establishes stealth connection with a site hosting the malign program. That’s how the installation of the HELP_HELP_HELP virus is triggered. Then, the contagion materializes itself on the target machine by first running a scan for various types of data. Given the essence of any crypto ransomware, it’s clear what the scan is aimed at – that’s how the infection obtains a list of the victim’s personal files to be locked down. The data categories at stake include all sorts of documents, pictures, videos, databases, backups and many other formats. To perform the crypto part, the perpetrating program connects to a C2 server over UDP port and requests a unique encryption key. Cerber moves on by applying an unbeatable cipher to personal files so that the user is no longer able to access them. A byproduct of this routine is the tweaking of filenames – the Trojan replaces them with 10 hexadecimal characters and affixes a 4-character extension derived from the PC’s MachineGuid value.
After the data mutilation phase of the compromise has been fulfilled, the ransomware sets a new desktop wallpaper without asking for the user’s consent. This is actually a JPG edition of the ransom notes. Another one is called _HELP_HELP_HELP_[random].hta, where the part in brackets is an 8-character string that identifies a specific victim in Cerber’s system. The ransom notes instruct the user to download and install the anonymity-oriented Tor Browser and visit their personal decryption page by entering a specified .onion URL in the browser. The Cerber Decryptor page provides the size of the ransom to submit for file decoding, the appropriate Bitcoin address, and the amount of time left before the ransom increases.
Sticking to the walkthrough imposed by the ransomware is the last thing to do. If Cerber has attacked a computer, trying to recover files beyond the crypto route is strongly recommended. The steps below will give you an idea of the optimal alternative for this purpose.
HELP_HELP_HELP ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download HELP_HELP_HELP ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by HELP_HELP_HELP ransomware
Workaround 1: Use file recovery software
It’s important to know that the HELP_HELP_HELP ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether HELP_HELP_HELP ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓