How to remove WannaCry ransomware and decrypt .WNCRY files
A ransomware strain called WannaCry is hitting the headlines of the world’s leading security resources. Such a close attention is for a reason. This infection has attacked a nuWNCRY file ransomware removermber of large companies in Europe over the past few days, and it keeps making the rounds in a steady fashion. The ransom Trojan encrypts its targets’ proprietary data records and blemishes them with the .WNCRY file extension.
Table of Contents
What is the WannaCry ransomware?
The .WNCRY file virus, which also manifests itself as Wana Decrypt0r 2.0, represents a relatively new lineage of crypto threats. On the outside, it looks similar to its precursor called WCRY, or Wanna Decryptor 1.0. It took the architects of this campaign a little more than a month to release an updated version of their plague. The latest variant proved to be much more complex and robust in terms of the propagation, encryption mechanism and extortion techniques. The rapidity of its circulation is unprecedented – it reportedly contaminated a whopping 57,000 computers over the course of only several hours on May 12, 2017. This prevalence is explained by the fact that the cybercriminals are using NSA exploits dumped by hackers earlier this month. This way, the felons are able to access workstations remotely via RDP and run the ransomware without having to social engineer the victims.
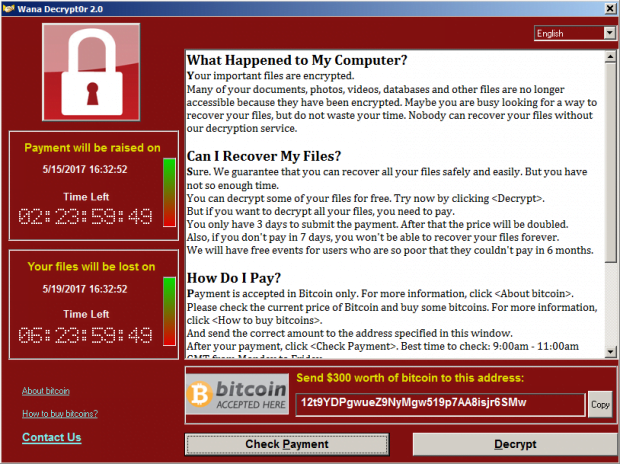
Identifying this strain is fairly prosaic. Having completed the contamination chain, it configures the target system to display a new desktop background with a warning message on it. Furthermore, a screen titled Wana Decrypt0r 2.0 pops up, providing details of what happened and displaying the amount of time during which the ransom must be submitted. The information in this window also includes the size of the ransom, which is the Bitcoin equivalent of $300, as well as the Bitcoin address to send the digital cash. Another conspicuous hallmark of the assault is a new file extension added to encrypted data. The list of possible extensions at this point includes .WNCRY, .WCRY, .WNRY, and .WNCRYPT. The first one, .WNCRY, is most frequently encountered during this particular ransomware wave. The original filenames are not changed, so victims are confronted with the following transformation of a sample file: Chart.xlsx – Chart.xlsx.WNCRY.
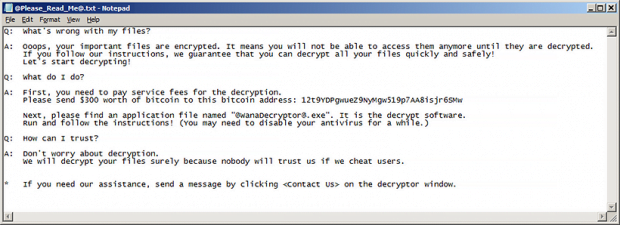
The WannaCry ransomware also leaves a plaintext ransom note to make sure the victim won’t fail to find the decryption walkthrough imposed by the attackers. It’s named @Please_Read_Me@.txt. The wording in it is slightly different than on the above-mentioned warning window. It says, “What’s wrong with my files? Oooops, your important files are encrypted. It means you will not be able to access them anymore until they are decrypted. If you follow our instructions, we guarantee that you can decrypt all your files quickly and safely.” Long story short, the recovery method suggested by the crooks presupposes that the user must pay $300 worth of Bitcoin and then run an application called @wanadecryptor@.exe, which is dropped onto the computer as part of the attack.
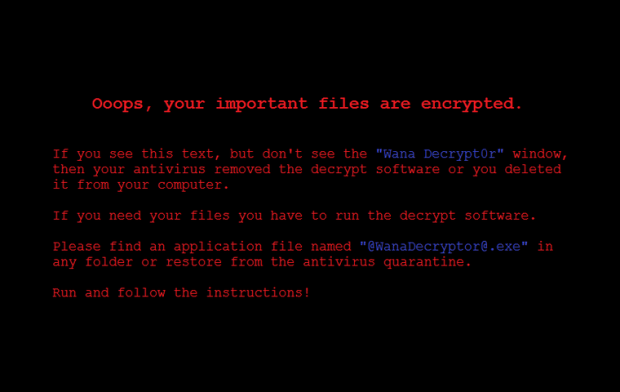
To protect itself from being terminated, the WannaCry virus displays a few tips on the new desktop wallpaper. It provides steps applicable if the victim’s antimalware suite had removed the Wana Decrypt0r tool. The desktop message specifies instructions to re-launch the malicious executable in order to be able to proceed with decryption through payment. All in all, the attack looks well-thought-out no matter how you slice it, which suggests that the campaign is being operated by threat actors with significant extortion background. The technically complex distribution via RDP poses another evidence that the crooks aren’t rookies in what they are doing. So the security industry is facing another skilled adversary, and hopefully the white hats will contrive a countervailing methodology sometime soon.
Meanwhile, WannaCry keeps infecting organizations and end users on a large scale. Some of the reported victims include a Spanish telco provider and a number of UK healthcare institutions. Of course, the best defense is not to get infected in the first place. If the compromise has occurred, the instructions below are the starting point for troubleshooting.
WannaCry ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download WannaCry ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by WannaCry ransomware
Workaround 1: Use file recovery software
It’s important to know that the WannaCry ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether WannaCry ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓