Thor file: restore encrypted .thor extension files
Thor is the latest persona of the infamous Locky ransomware. This variant was released less than a day after the previous .shit extension edition was discovered, which might suggest that the latter was a misunderstanding in the cybercriminal ring responsible for this lineage. The updated pest doesn’t have many adjustments inside. It appends .thor to all encrypted files, creates _WHAT_is.html and _WHAT_is.bmp recovery help files, and demands about half a Bitcoin for decryption.
Table of Contents
What is the Thor ransomware?
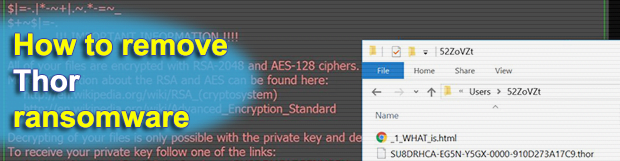
There has been some abnormal activity around the Locky family of file-encrypting ransomware lately. Having rolled out an update with a blatant bad language component a couple of days ago, the extortionists promptly switched to a new one. This change is off the beaten track for the syndicate in question, because it typically takes the crooks a month or so to come up with code tweaks like that. What’s new in the most recent version? First off, it’s the .thor extension that the ransomware has begun to concatenate to scrambled files. The ransom notes used in the current campaign have assumed different names as well. It adds the following files to instruct victims on recovery options: _WHAT_is.html, [random_numeric_value]_WHAT_is.html, and _WHAT_is.bmp. These can be found on the desktop, with the HTML copy being also created inside various folders. The desktop background undergoes a change too, displaying a few preliminary directions to start the decryption process.
The Thor ransomware is proliferating by means of a well-orchestrated social engineering campaign. Those in charge leverage a botnet to generate thousands of phishing emails daily, sending them to individual users and executives of multiple organizations. The emails pretend to deliver invoices, receipts, package details, local representation offers, budget-related spreadsheets and the like. Most of the attachments are ZIP files that contain obfuscated JS or VBS entities inside. The criminals tend to use a double extension trick, where a dangerous executable looks like a harmless Microsoft Office or PDF document. Once a user opens one of these attached documents, the infection workflow commences with downloading a DLL installer. This object, in its turn, performs the rest of the ransomware deployment process in a stealthy way.
Then, Thor scans mapped and unmapped network shares, removable drives and, of course, the local hard disk in order to find the user’s personal data. This routine revolves around file extensions hard-coded into the Trojan that correspond to the most widespread data formats. By using a tandem of RSA and AES algorithms, the pest locks down the prey’s information in seconds. Interestingly, this edition of Locky can encrypt the spotted files without querying its Command and Control server for unique cryptographic keys. This offline operation principle is relatively new to the ransomware world. It allows the offending code to evade Firewall and AV blocking more effectively than before.
In addition to the crypto impact, the infection renames one’s files to strings like AU5DRJBS-FG4M-GX4Y-10F6-0A9146A80710.thor. Such a take on data crippling makes it impossible to locate a specific file by its new look. The above-mentioned help manuals recommend the victim to visit a Tor-based resource called the Locky Decryptor Page for concise instructions. The page says how much to pay for the private RSA key and the decrypt tool – usually 0.5 Bitcoin, although some users have reported much larger amounts reaching 3.5 Bitcoins. This situation is close to a stalemate, but fortunately there are several options for bypassing the Thor ransomware grip.
Thor extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Thor extension
Workaround 1: Use file recovery software
It’s important to know that the Thor extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Thor extension has been completely removed
Again, file removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓



