Osiris ransomware: decrypt and remove .osiris file virus

The Locky ransomware family continues to spawn new mutated extortion programs. Its developers are evidently experimenting with payload delivery and data crippling practices. This time, the perpetrators have created another spinoff of their nefarious prototype that adds the .osiris extension to encrypted files and drops the OSIRIS-[victim_ID].htm ransom note.
Table of Contents
What is the Osiris ransomware?
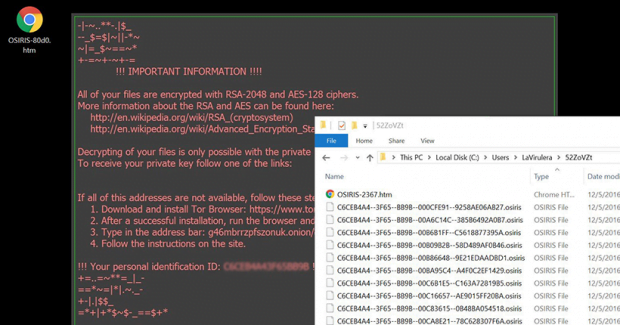
In cybersecurity terms, the word “Osiris” has come to denote an alias of the nasty Locky ransomware rather than something that has to do with the mythology of ancient Egypt. The latest malicious sample from the slew of this family’s variants boasts an intricate contamination technique, a different file renaming pattern, and a new format of the recovery manual. This edition concatenates the .osiris extension to every file that is subject to the military-grade encryption through an uncrackable mixture of RSA and AES standards. The revamped ransom Trojan also affects filenames in a new way, replacing them with entries like B5F7GEC2–A9BF–816E–373B5CBG–41019FD253D9.osiris. The algorithm is [8_hexadecimal_chars]–[4_hexadecimal_chars]–[4_hexadecimal_chars]–[8_hexadecimal_chars]–[12_hexadecimal_chars].osiris.
Another change that victims won’t fail to notice is that the ransomware creates the help files in a single format (HTM), whereas its precursors used to drop several different ransom note variants. The recovery walkthrough is now explained in OSIRIS-[victim_ID].htm document. The unique identifier in its name will usually consist of 4 characters. Furthermore, it is going to be different for copies of the file left the desktop and the ones embedded in individual folders with skewed personal files.
The HTM decryption avenue contains a hyperlink to the victim’s personal recovery hub titled the Locky Decryptor Page. The .onion link can only be loaded with the Tor Browser, which poses a layer of anonymity for the ransomware distributors. Therefore, it’s necessary to download and install this browser to proceed. When on the page, the infected user gets the following information: the size of the ransom, the Bitcoin wallet address to send the digital cash to, as well as some resources to purchase Bitcoins. The decryption service imposed by the attackers will normally cost 0.5 BTC, or some 370 USD. However, making deals with ransomware operators is a slippery slope, which is why it’s a much better idea to try some of the best forensic practices of data recovery.
Just like its antecedents, the Osiris edition of Locky makes its way onto one’s computer through spam. The only novelty in the current spam wave is that the booby-trapped email attachment is an XLS document. This file will return a popup that recommends the recipient to enable macros. If the user turns out gullible enough to opt for this, the infection will exploit a known macros vulnerability and launch the ransomware. So, be sure to treat eye-catching email attachments with a reasonable degree of mistrust.
Osiris extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Osiris extension
Workaround 1: Use file recovery software
It’s important to know that the Osiris extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Osiris extension has been completely removed
Again, file removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓