Target Attacks on Warranties for Fun and Profit

This talk is “Not-So-Limited Warranty: Target Attacks on Warranties for Fun and Profit.” This talk is for people who like unconventional forms of social engineering, who want to learn more about serial numbers and how they’re used to protect products, and people who enjoy finding holes, of course. This isn’t for anyone who works for/with Amazon, Apple, Lenovo or Procter & Gamble (Pringles).
Who am I? I’m a student; I’ll be a senior in fall, so, shortly. I’m a warranty enthusiast – you know, everyone loves reading 6-page paragraphs when you get a new device. I do a little programming on the side. There’s my email if you ever want to email me.
Table of Contents
What is a serial number?
 A serial number is used to identify a product. If you have the serial number, you’re basically considered the owner of the product. There’s different types of serial numbers. For example, there’s the identifying, which will contain 2012 – it was made in 2012, or there’s the random, which is – I don’t know who came up with an idea of using random numbers, but those are out there. And there are sequentials; sequentials are used in food, so you can track reduction and such, and that’s 123, you know what a sequential is.
A serial number is used to identify a product. If you have the serial number, you’re basically considered the owner of the product. There’s different types of serial numbers. For example, there’s the identifying, which will contain 2012 – it was made in 2012, or there’s the random, which is – I don’t know who came up with an idea of using random numbers, but those are out there. And there are sequentials; sequentials are used in food, so you can track reduction and such, and that’s 123, you know what a sequential is.
They’re usually located on a product, in physically accessible area in case it malfunctions. If you have a computer something and it stops turning on, you really don’t want the serial only accessible via internal means, though sometimes it’s available via software, like on iPhones or some Apple products.
Why are serial numbers important?
 Proof of ownership: I can now cancel your warranty by saying: “I do not agree to those terms and conditions that are in this wonderful 6-page paragraph.” And there is the Die Hard movie plot where the evil hackers are working on invalidating everyone’s warranty to collapse the economy. You can do information disclosure; you can disclose quite a bit of information with just an Apple cell phone serial. I’ve got some C# code for that that I can show you, guys, in a couple. You can report it stolen – that’s always great fun.
Proof of ownership: I can now cancel your warranty by saying: “I do not agree to those terms and conditions that are in this wonderful 6-page paragraph.” And there is the Die Hard movie plot where the evil hackers are working on invalidating everyone’s warranty to collapse the economy. You can do information disclosure; you can disclose quite a bit of information with just an Apple cell phone serial. I’ve got some C# code for that that I can show you, guys, in a couple. You can report it stolen – that’s always great fun.
The C# code here – basically, this code generates an iPhone serial and then automatically plugs it in to this wonderful hole that Apple left on their website that will return all kinds of fun data like ICCID, IEMI, personalization, date of purchase, carrier, whether it is covered by warranty – all kinds of fun, juicy information that you can use.
How can people get serial numbers?
 The Internet, Google Images: you run a search for ex-item, and wherever the serial number is located, and I guarantee you’re going to find at least 10. Calling people on Graigslist or eBay: you ask them if it’s stolen, so you ask for the serial number, now you’ve got a serial number. Stores: you go on to the store, you flip your laptop upside down, and you’ve got the serial number. Guessing: sequential serials are terrible; if I could find one, I found all of them. Or owning the product is the case with some people.
The Internet, Google Images: you run a search for ex-item, and wherever the serial number is located, and I guarantee you’re going to find at least 10. Calling people on Graigslist or eBay: you ask them if it’s stolen, so you ask for the serial number, now you’ve got a serial number. Stores: you go on to the store, you flip your laptop upside down, and you’ve got the serial number. Guessing: sequential serials are terrible; if I could find one, I found all of them. Or owning the product is the case with some people.
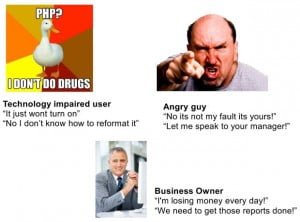 Personal touches are everything when you’re dealing with customer’s support. Personally, a technology impaired user works quite well with tech support, because they’re underpaid and undertrained, and, frankly, they just want to go home at the end of the day, but if someone who can’t figure out how to boot their phone is busy keeping them at the office, they’re pretty much going to screw you along. The angry guy, who is pretty self-explanatory, and the business owner who needs this back online right now for the reports.
Personal touches are everything when you’re dealing with customer’s support. Personally, a technology impaired user works quite well with tech support, because they’re underpaid and undertrained, and, frankly, they just want to go home at the end of the day, but if someone who can’t figure out how to boot their phone is busy keeping them at the office, they’re pretty much going to screw you along. The angry guy, who is pretty self-explanatory, and the business owner who needs this back online right now for the reports.
Examples of security
The next couple of slides I’ve ranked a couple of companies on security. Protection is how they secure it and how these countermeasures are not easily broken (higher score is better), and how obnoxious it is if someone was actually returning a device to get it repaired or replaced or something (lover is better).
Pringles
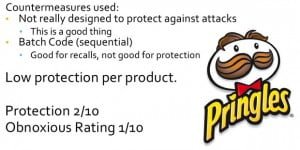 Starting, we got Pringles. Pringles wasn’t really designed to protect against targeted attacks like this, because no one really wants to go out there and get Pringles. So they have a batch code, which is sequential, and that makes perfect sense if you’re going to have a food recall, or otherwise something in manufacturing goes wrong. And this is low protection per product, and it’s not very obnoxious, it’s not intrusive at all, easily bypassed.
Starting, we got Pringles. Pringles wasn’t really designed to protect against targeted attacks like this, because no one really wants to go out there and get Pringles. So they have a batch code, which is sequential, and that makes perfect sense if you’re going to have a food recall, or otherwise something in manufacturing goes wrong. And this is low protection per product, and it’s not very obnoxious, it’s not intrusive at all, easily bypassed.
Lenovo
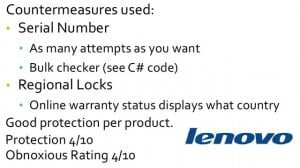 Lenovo will use a serial number, but luckily they’re nice enough to give us unlimited attempts on an online validator. If that wasn’t enough, you’ve got a bulk checker, so you can upload a .csv file with as many as you want and just check them. I’ve got some: this file will permutate through it if you have a base string, which is half of the serial. It will permutate through and give you every combination of that serial, and then you can go forth and upload the .csv file to the link included in the code. This code should be on your disks. You can upload it to there, and then you can get the country, the warranty information, the model, the year – any information you want about his product. So, that’s kind of a big hole. Regional locks: they lock it down based on country, which only really works if you don’t have an online validator that tells you the country of the serial every time you check it. This is OK protection, I mean, it will keep some people out; it’s not really that obnoxious.
Lenovo will use a serial number, but luckily they’re nice enough to give us unlimited attempts on an online validator. If that wasn’t enough, you’ve got a bulk checker, so you can upload a .csv file with as many as you want and just check them. I’ve got some: this file will permutate through it if you have a base string, which is half of the serial. It will permutate through and give you every combination of that serial, and then you can go forth and upload the .csv file to the link included in the code. This code should be on your disks. You can upload it to there, and then you can get the country, the warranty information, the model, the year – any information you want about his product. So, that’s kind of a big hole. Regional locks: they lock it down based on country, which only really works if you don’t have an online validator that tells you the country of the serial every time you check it. This is OK protection, I mean, it will keep some people out; it’s not really that obnoxious.
Amazon (Kindles)
 Moving on: Amazon. They use a serial number, which is not sequential and actually follows a preset set of rules. But once again they give us unlimited attempts to register it on an Amazon account, so we could, I don’t know, automate the system and start registering as many false serials as we wanted. Oh, and every time you get a serial right, it gives you a free month of Amazon Prime in case you need a bonus or something. When it comes time to actually send a product back, they put a hold on your credit card, a whopping $2, so if you have a VISA gift card, you can easily circumvent this. This is really over the top protection that doesn’t work, and it’s kind of obnoxious too.
Moving on: Amazon. They use a serial number, which is not sequential and actually follows a preset set of rules. But once again they give us unlimited attempts to register it on an Amazon account, so we could, I don’t know, automate the system and start registering as many false serials as we wanted. Oh, and every time you get a serial right, it gives you a free month of Amazon Prime in case you need a bonus or something. When it comes time to actually send a product back, they put a hold on your credit card, a whopping $2, so if you have a VISA gift card, you can easily circumvent this. This is really over the top protection that doesn’t work, and it’s kind of obnoxious too.
Apple
 Apple uses serial numbers that are once again not sequential. They’re easy to generate: I included the generation of them in the C# code, the same that queries the website. They ask for ICCID and IEMI upon replacement. Once again, an attacker can circumvent this by querying the script that they so generously provided on their server. The one part where they will actually keep most people down is a credit card on hold: they charge the full amount of the product to your credit card, so this kind of makes them very well protected, but in turn it makes them quite obnoxious, because not everyone’s got a foothold.
Apple uses serial numbers that are once again not sequential. They’re easy to generate: I included the generation of them in the C# code, the same that queries the website. They ask for ICCID and IEMI upon replacement. Once again, an attacker can circumvent this by querying the script that they so generously provided on their server. The one part where they will actually keep most people down is a credit card on hold: they charge the full amount of the product to your credit card, so this kind of makes them very well protected, but in turn it makes them quite obnoxious, because not everyone’s got a foothold.
Protecting companies
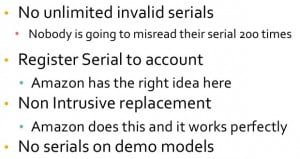 Protecting companies: no unlimited invalid serials; no one is going to misread their serial, their Kindle serial to activate 200 times a day. I mean, a captcha could save so many of these. Register the serial to a single account, and a single account only. Amazon has the right idea here by linking it to your Amazon.com account, but they still let you have unlimited attempts. No serials on demo models: if you’re going to put a demo of your product in a store, you really shouldn’t have a serial number; just scratch it off or otherwise remove it. And no automated checking systems, because that’s a bad idea.
Protecting companies: no unlimited invalid serials; no one is going to misread their serial, their Kindle serial to activate 200 times a day. I mean, a captcha could save so many of these. Register the serial to a single account, and a single account only. Amazon has the right idea here by linking it to your Amazon.com account, but they still let you have unlimited attempts. No serials on demo models: if you’re going to put a demo of your product in a store, you really shouldn’t have a serial number; just scratch it off or otherwise remove it. And no automated checking systems, because that’s a bad idea.
Credits to my friends Jared “Revelation” M. and Niko “Lulzpid” R.
Posted in: News
Leave a Comment (0) ↓