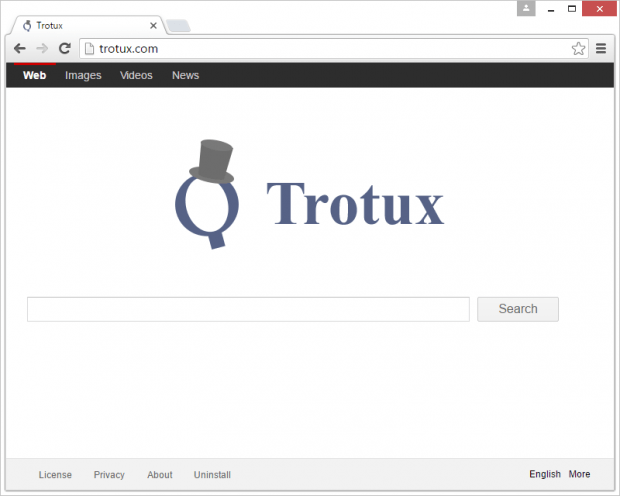
Remove Trotux virus from Chrome, Firefox and IE
Not every computer application that’s bundled with other software is malicious. For instance, millions of Windows users are regularly encountering Adobe Flash Player updates, where third-party products are included in the default installation routine. There is an offending facet of such packaging, though. Trotux is a potentially unwanted browser extension distributed along with some freeware in a furtive way.
Albeit there is no immediate harm in visiting Trotux.com directly from one’s web browser, the repeated popping of that page on its own typically indicates a security issue. This may be an aftermath of a stealthy contamination of the PC, where the original Internet surfing preferences are tweaked without the consent of whoever is the admin on the system. The likely troublemaker is an add-on with cross-browser functionality that modifies the homepage, default search and new tab settings automatically. To add insult to injury, this rogue browser helper object will affect the configuration of shortcuts for random programs installed on the machine, thus forcing hits to Trotux.com whenever these utilities are opened.
Prior to the occurrence of these symptoms, the user runs a setup of some cheesy software. The above-mentioned bundling mechanism of adware distribution is heavily exploited for the proliferation of Trotux. The commonplace scenario is where an unsuspecting person looks for or accidentally stumbles upon a fancy-looking free media player, streaming video grabber or file downloader that’s loaded with the drive-by. When installing one of these booby-trapped products, most people don’t look too carefully at the extra offers included into the so-called “express”, or default, setup. That’s usually where the Trotux virus payload sits. Therefore, unless the original preset of such installs is modified and redundant entities deselected, the adware will get in and start wreaking havoc with the computer.
First, the obtrusive extension is automatically added to Chrome, Firefox and possibly other browsers used on the computer. This new entry does not ask for user permission while changing the main custom settings in these browsers. Also, the adware creates a scheduled task to check for manual modifications on the user’s end, and if it detects any it restores the wrong ones automatically.
Consequently, the victim will keep visiting Trotux.com, which is a web page that seems to be designed according to the best practices of online search. It is a pseudo search engine, though. Instead of returning results of its own, Trotux reroutes the user to another provider. However, every instance of hitting this site is logged, and the scoundrels are thus able to monetize this traffic. To resolve the issue, be sure to follow the tips below and get rid of the adware proper along with the adverse browser impact.
Table of Contents
Trotux adware automatic removal
The extermination of Trotux hijacker can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the adware removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the adware is gone for good.
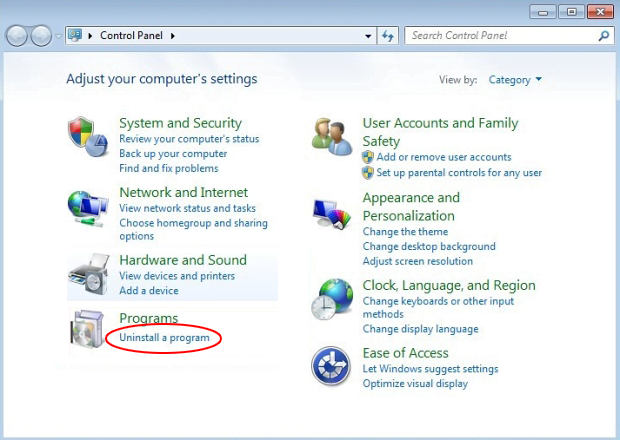
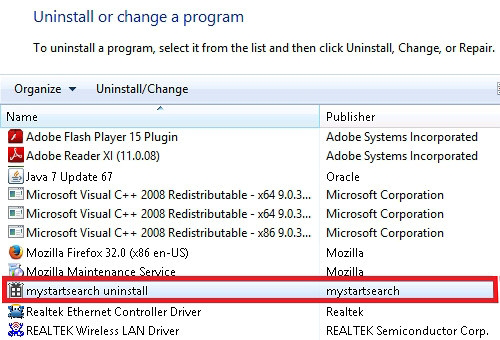
Remove Trotux adware using Control Panel
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Trotux adware removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
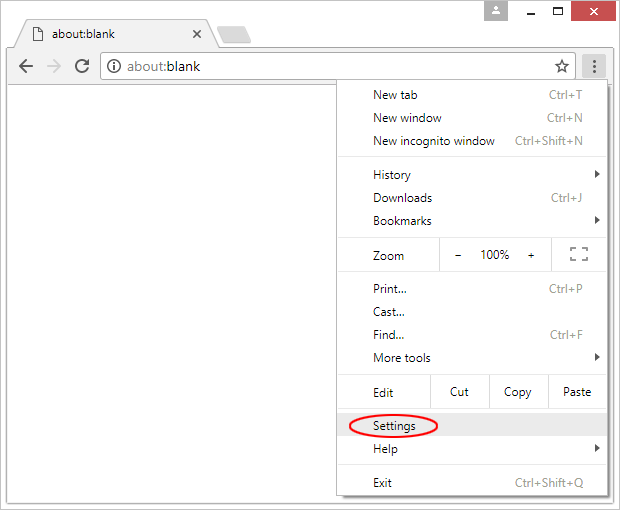
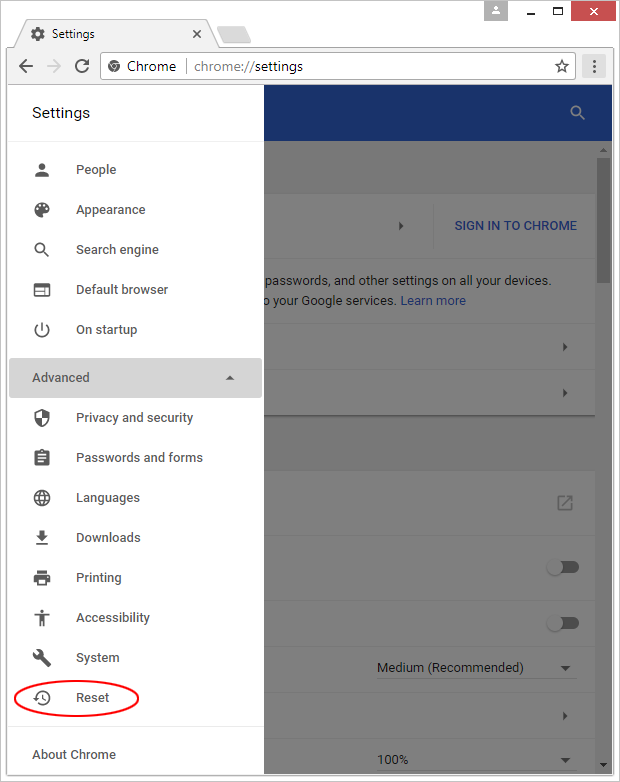
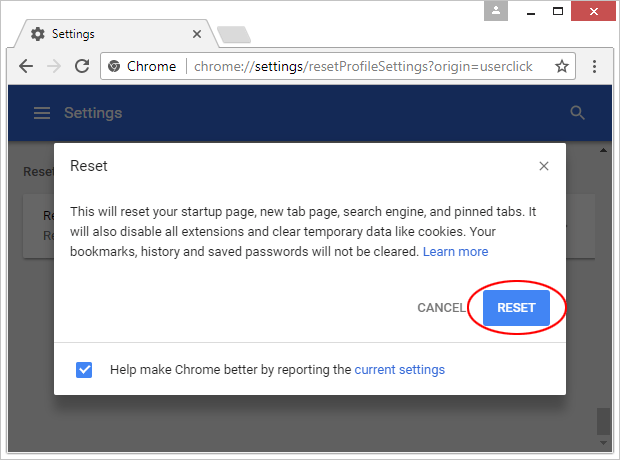
Reset Google Chrome
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

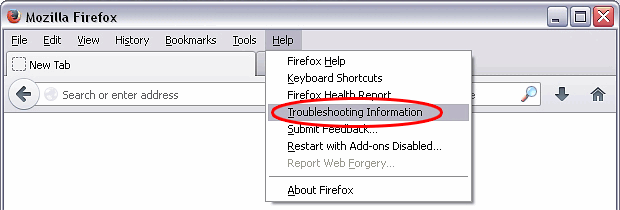
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

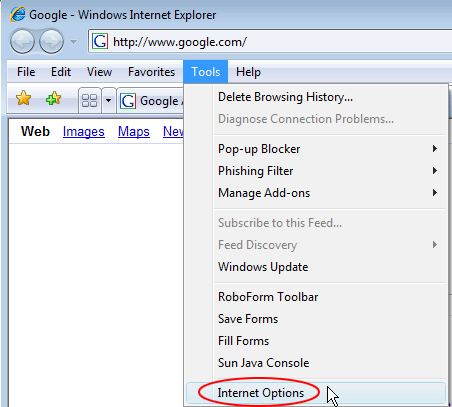
Reset Internet Explorer
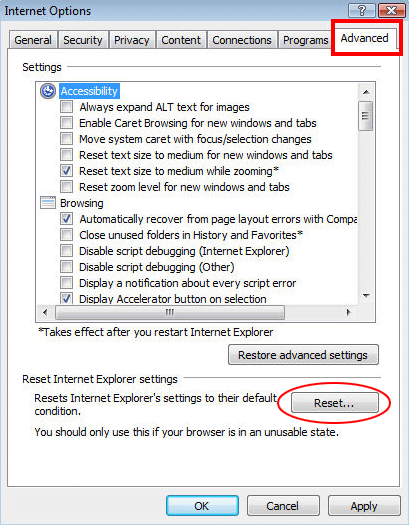
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

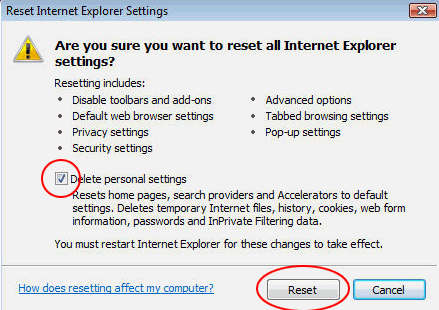
- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether Trotux adware has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this hijacker are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓